Top Stories
Recent Posts
-

The Gentlemen Ransomware Claims 478 Victims, Can Spread Like a Worm
A new analysis of The Gentlemen operation has revealed that the financially…
-

Cybersecurity Stars Awards 2026: Winners Announced Across 95 Categories
Most good security work is invisible by design. Today is the exception.…
-
ThreatsDay Bulletin: Worm Code Leaked, AI Agent Phished, Claude Action Patch + 28 New Stories
It’s been one of those weeks. You expect the usual noise: recycled…
-

AI Broke Vulnerability Management. That’s Why CISOs Are Moving Budget to BAS.
For thirty years, vulnerability management ran on a buffer: the months between…
-

GitHub to Disable npm Install Scripts by Default to Stop Supply Chain Attacks
GitHub has announced what it said are “breaking changes” coming to npm…
-
China-Linked JDY Botnet Expands to 1,500+ Devices for Cyber Reconnaissance
Cybersecurity researchers have warned of a “resurgence and expansion” of JDY, a…
-

Unpatched Langflow Flaw CVE-2026-5027 Exploited for Unauthenticated RCE
A high-severity unpatched security flaw in Langflow, an open-source low-code platform to…
-
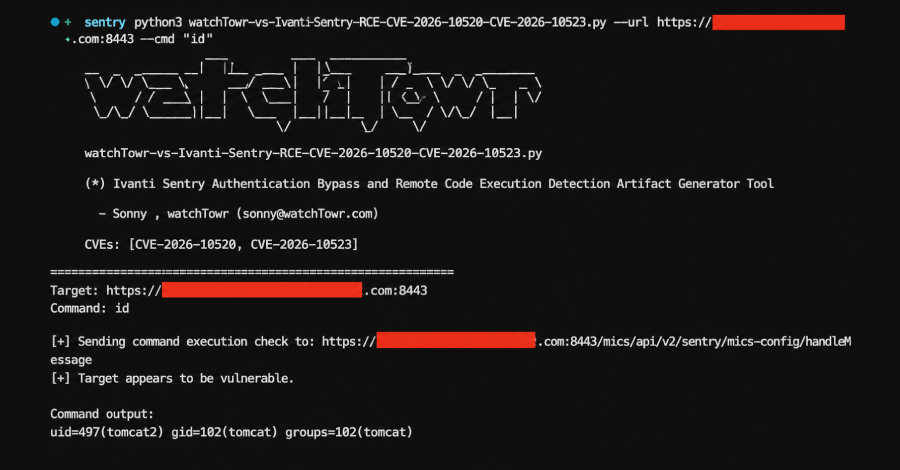
Ivanti, Fortinet, and SAP Release Patches for Multiple Critical Vulnerabilities
Fortinet, Ivanti, and SAP have released security updates to address multiple critical…
-

Your Automated Pentest Looks Clean. See What It Missed in This Expert Webinar
Your pentest report looks clean. That might be the problem. Run automated…
-

ServiceNow Flaw Exploited to Gain Unauthorized Access to Customer Instances
ServiceNow has warned about a security incident in which unknown threat actors…