
Salesforce Patches Critical ForcedLeak Bug Exposing CRM Data via AI Prompt Injection
Cybersecurity researchers have disclosed a critical flaw impacting Salesforce Agentforce, a platform for building artificial intelligence (AI) agents, that could…

Cybersecurity researchers have disclosed a critical flaw impacting Salesforce Agentforce, a platform for building artificial intelligence (AI) agents, that could…

The North Korea-linked threat actors associated with the Contagious Interview campaign have been attributed to a previously undocumented backdoor called…
The latest Gcore Radar report analyzing attack data from Q1–Q2 2025, reveals a 41% year-on-year increase in total attack volume….

Cybersecurity researchers have discovered two malicious Rust crates impersonating a legitimate library called fast_log to steal Solana and Ethereum wallet…

A suspected cyber espionage activity cluster that was previously found targeting global government and private sector organizations spanning Africa, Asia,…
Companies in the legal services, software-as-a-service (SaaS) providers, Business Process Outsourcers (BPOs), and technology sectors in the U.S. have been…

Most businesses don’t make it past their fifth birthday – studies show that roughly 50% of small businesses fail within…

Cloud security company Wiz has revealed that it uncovered in-the-wild exploitation of a security flaw in a Linux utility called…

Libraesva has released a security update to address a vulnerability in its Email Security Gateway (ESG) solution that it said…
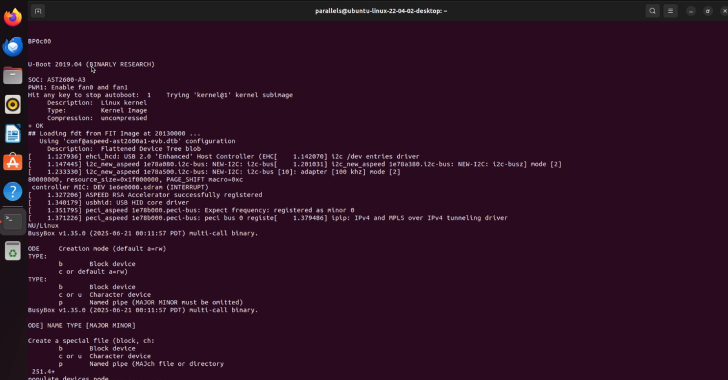
Cybersecurity researchers have disclosed details of two security vulnerabilities impacting Supermicro Baseboard Management Controller (BMC) firmware that could potentially allow…