Is Your Google Workspace as Secure as You Think it is?
The New Reality for Lean Security Teams If you’re the first security or IT hire at a fast-growing startup, you’ve…
The New Reality for Lean Security Teams If you’re the first security or IT hire at a fast-growing startup, you’ve…

A European embassy located in the Indian capital of New Delhi, as well as multiple organizations in Sri Lanka, Pakistan,…
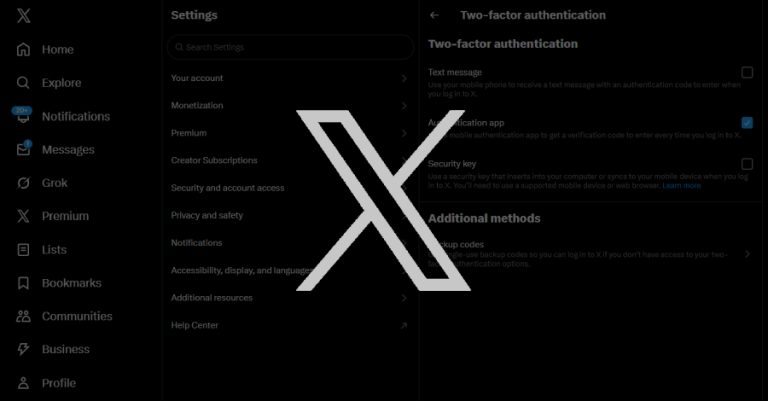
Social media platform X is urging users who have enrolled for two-factor authentication (2FA) using passkeys and hardware security keys…

Security, trust, and stability — once the pillars of our digital world — are now the tools attackers turn against…

The threat actors behind a large-scale, ongoing smishing campaign have been attributed to more than 194,000 malicious domains since January…

Microsoft on Thursday released out-of-band security updates to patch a critical-severity Windows Server Update Service (WSUS) vulnerability with a proof-of-concept…

A Pakistan-nexus threat actor has been observed targeting Indian government entities as part of spear-phishing attacks designed to deliver a…
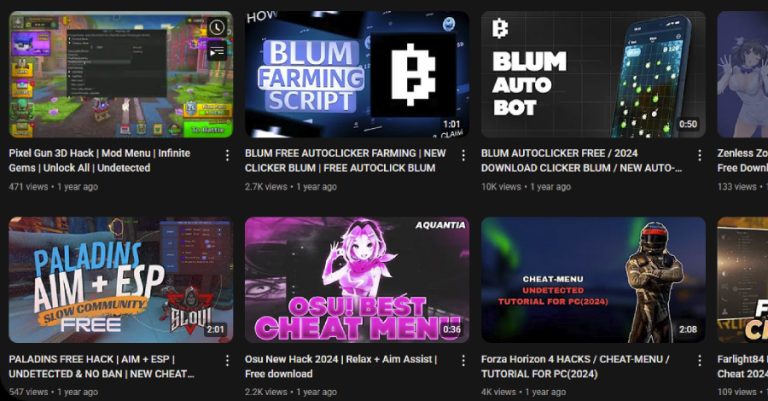
A malicious network of YouTube accounts has been observed publishing and promoting videos that lead to malware downloads, essentially abusing…

Cybersecurity researchers have discovered a self-propagating worm that spreads via Visual Studio Code (VS Code) extensions on the Open VSX…

Threat actors with ties to North Korea have been attributed to a new wave of attacks targeting European companies active…