
Why Organizations Are Abandoning Static Secrets for Managed Identities
As machine identities explode across cloud environments, enterprises report dramatic productivity gains from eliminating static credentials. And only legacy systems…

As machine identities explode across cloud environments, enterprises report dramatic productivity gains from eliminating static credentials. And only legacy systems…

E-commerce security company Sansec has warned that threat actors have begun to exploit a recently disclosed security vulnerability in Adobe…

The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Wednesday added a critical security flaw impacting Motex Lanscope Endpoint Manager…

The Iranian nation-state group known as MuddyWater has been attributed to a new campaign that has leveraged a compromised email…
Government, financial, and industrial organizations located in Asia, Africa, and Latin America are the target of a new campaign dubbed…
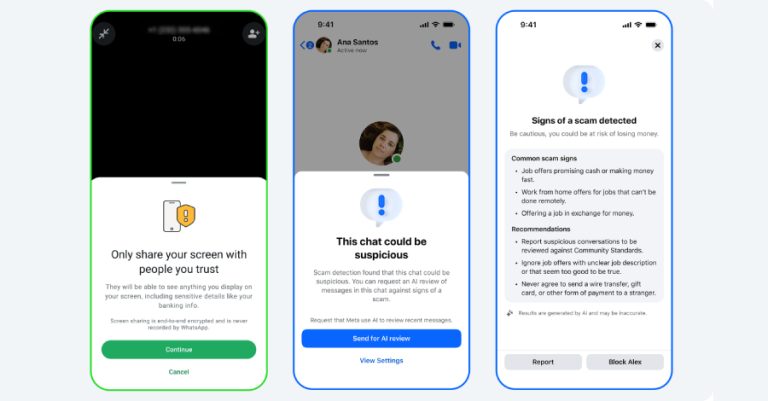
Meta on Tuesday said it’s launching new tools to protect Messenger and WhatsApp users from potential scams. To that end,…

Artificial intelligence (AI) holds tremendous promise for improving cyber defense and making the lives of security practitioners easier. It can…

A European telecommunications organization is said to have been targeted by a threat actor that aligns with a China-nexus cyber…
A new malware attributed to the Russia-linked hacking group known as COLDRIVER has undergone numerous developmental iterations since May 2025,…

The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Monday added five security flaws to its Known Exploited Vulnerabilities (KEV)…