Chinese Hackers Exploit ArcGIS Server as Backdoor for Over a Year
Threat actors with ties to China have been attributed to a novel campaign that compromised an ArcGIS system and turned…
Threat actors with ties to China have been attributed to a novel campaign that compromised an ArcGIS system and turned…
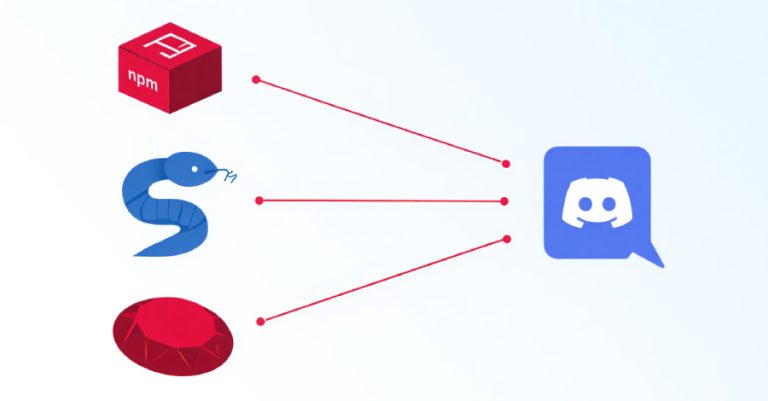
Cybersecurity researchers have identified several malicious packages across npm, Python, and Ruby ecosystems that leverage Discord as a command-and-control (C2)…

Every week, the cyber world reminds us that silence doesn’t mean safety. Attacks often begin quietly — one unpatched flaw,…
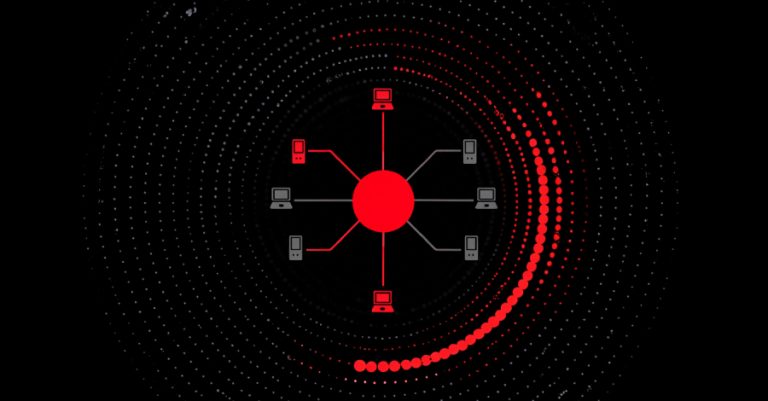
Malware campaigns distributing the RondoDox botnet have expanded their targeting focus to exploit more than 50 vulnerabilities across over 30…

Cybersecurity researchers have disclosed details of a new Rust-based backdoor called ChaosBot that can allow operators to conduct reconnaissance and…

Oracle on Saturday issued a security alert warning of a fresh security flaw impacting its E-Business Suite that it said…

Threat actors are abusing Velociraptor, an open-source digital forensics and incident response (DFIR) tool, in connection with ransomware attacks likely…
Cybersecurity researchers have disclosed details of an active malware campaign called Stealit that has leveraged Node.js’ Single Executable Application (SEA)…

The SOC of 2026 will no longer be a human-only battlefield. As organizations scale and threats evolve in sophistication and…

Cybersecurity company Huntress said it has observed active in-the-wild exploitation of an unpatched security flaw impacting Gladinet CentreStack and TrioFox…