
CISA Adds Actively Exploited XSS Bug CVE-2021-26829 in OpenPLC ScadaBR to KEV
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has updated its Known Exploited Vulnerabilities (KEV) catalog to include a security…

The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has updated its Known Exploited Vulnerabilities (KEV) catalog to include a security…
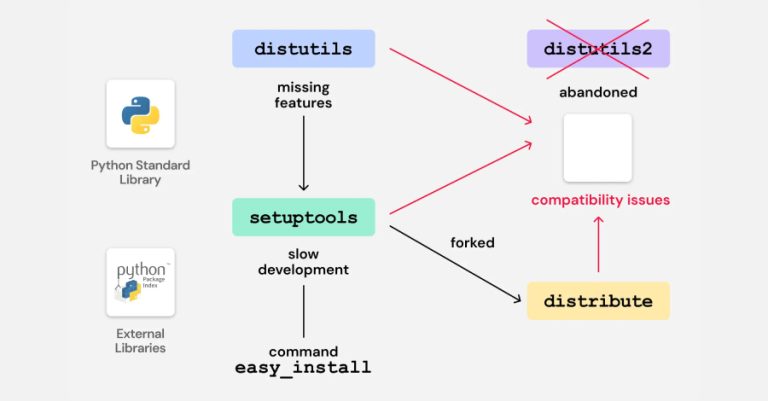
Cybersecurity researchers have discovered vulnerable code in legacy Python packages that could potentially pave the way for a supply chain…
The North Korean threat actors behind the Contagious Interview campaign have continued to flood the npm registry with 197 more…

As IT environments become increasingly distributed and organizations adopt hybrid and remote work at scale, traditional perimeter-based security models and…
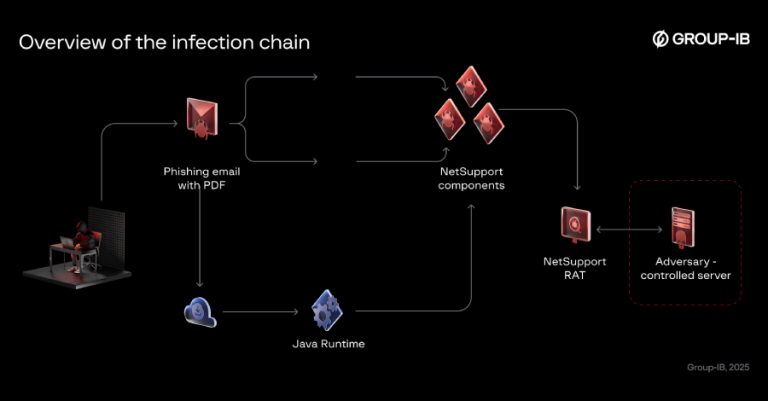
The threat actor known as Bloody Wolf has been attributed to a cyber attack campaign that has targeted Kyrgyzstan since…

If you’re using community tools like Chocolatey or Winget to keep systems updated, you’re not alone. These platforms are fast,…

Microsoft has announced plans to improve the security of Entra ID authentication by blocking unauthorized script injection attacks starting a…

Hackers have been busy again this week. From fake voice calls and AI-powered malware to huge money-laundering busts and new…

Gainsight has disclosed that the recent suspicious activity targeting its applications has affected more customers than previously thought. The company…

The second wave of the Shai-Hulud supply chain attack has spilled over to the Maven ecosystem after compromising more than…