
CISA Flags Actively Exploited Digiever NVR Vulnerability Allowing Remote Code Execution
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) added a security flaw impacting Digiever DS-2105 Pro network video recorders (NVRs)…

The U.S. Cybersecurity and Infrastructure Security Agency (CISA) added a security flaw impacting Digiever DS-2105 Pro network video recorders (NVRs)…

Fortinet on Wednesday said it observed “recent abuse” of a five-year-old security flaw in FortiOS SSL VPN in the wild…

The fraudulent investment scheme known as Nomani has witnessed an increase by 62%, according to data from ESET, as campaigns…
Every year, cybercriminals find new ways to steal money and data from businesses. Breaching a business network, extracting sensitive data,…

The U.S. Securities and Exchange Commission (SEC) has filed charges against multiple companies for their alleged involvement in an elaborate…

A law enforcement operation coordinated by INTERPOL has led to the recovery of $3 million and the arrest of 574…
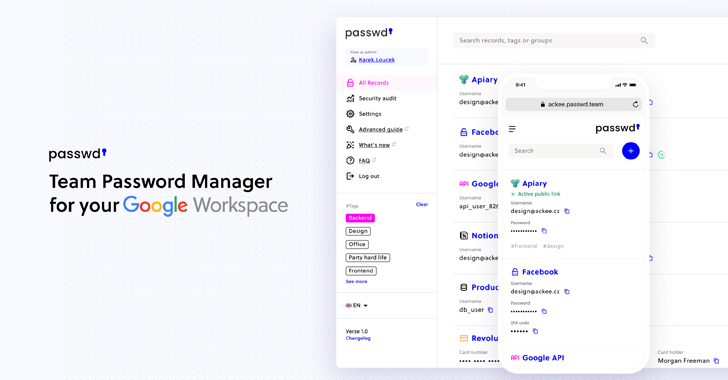
Passwd is designed specifically for organizations operating within Google Workspace. Rather than competing as a general consumer password manager, its…
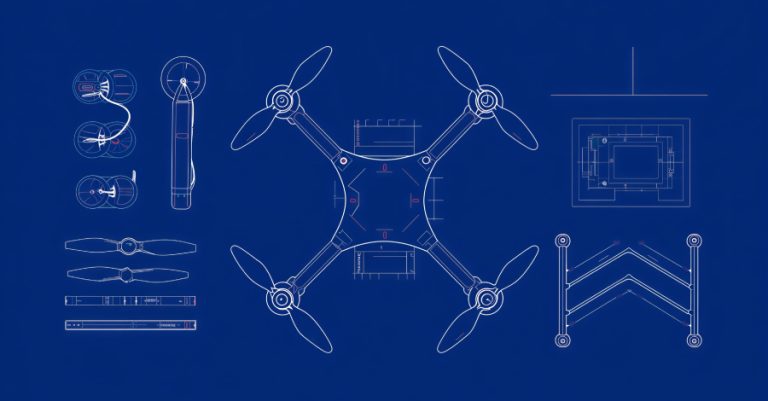
The U.S. Federal Communications Commission (FCC) on Monday announced a ban on all drones and critical components made in a…

Cyber threats last week showed how attackers no longer need big hacks to cause big damage. They’re going after the…

Threat actors have been observed leveraging malicious dropper apps masquerading as legitimate applications to deliver an Android SMS stealer dubbed…