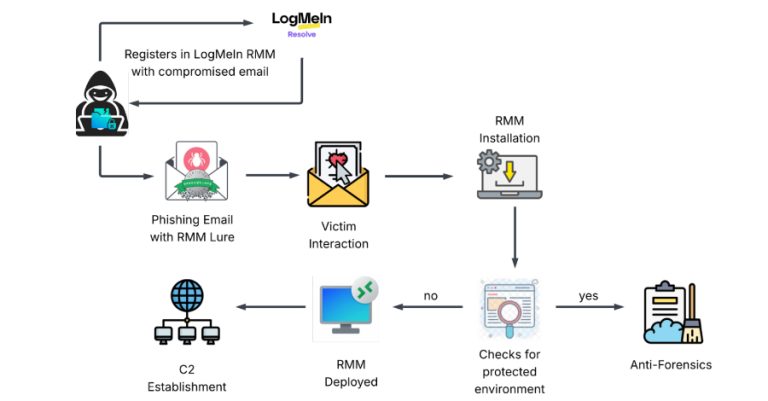
Phishing Attack Uses Stolen Credentials to Install LogMeIn RMM for Persistent Access
Cybersecurity researchers have disclosed details of a new dual-vector campaign that leverages stolen credentials to deploy legitimate Remote Monitoring and…
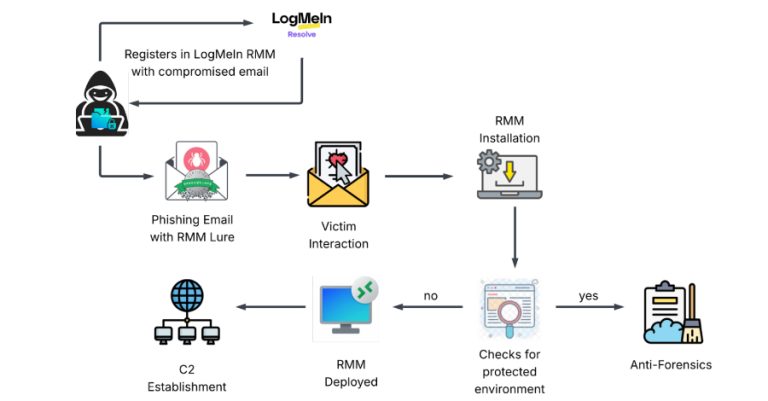
Cybersecurity researchers have disclosed details of a new dual-vector campaign that leverages stolen credentials to deploy legitimate Remote Monitoring and…
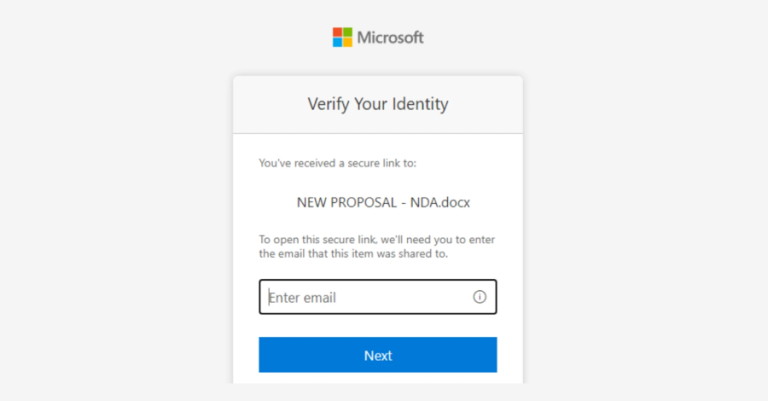
Microsoft has warned of a multi‑stage adversary‑in‑the‑middle (AitM) phishing and business email compromise (BEC) campaign targeting multiple organizations in the…
A critical security flaw has been disclosed in the GNU InetUtils telnet daemon (telnetd) that went unnoticed for nearly 11…
Security teams at agile, fast-growing companies often have the same mandate: secure the business without slowing it down. Most teams…

A new malicious package discovered in the Python Package Index (PyPI) has been found to impersonate a popular library for…

Cisco has released fresh patches to address what it described as a “critical” security vulnerability impacting multiple Unified Communications (CM)…
As many as 3,136 individual IP addresses linked to likely targets of the Contagious Interview activity have been identified, with…

Zoom and GitLab have released security updates to resolve a number of security vulnerabilities that could result in denial-of-service (DoS)…

Every managed security provider is chasing the same problem in 2026 — too many alerts, too few analysts, and clients…

A security vulnerability has been disclosed in the popular binary-parser npm library that, if successfully exploited, could result in the…