
LastPass Warns of Fake Maintenance Messages Targeting Users’ Master Passwords
LastPass is alerting users to a new active phishing campaign that’s impersonating the password management service, which aims to trick…

LastPass is alerting users to a new active phishing campaign that’s impersonating the password management service, which aims to trick…

The North Korean threat actors associated with the long-running Contagious Interview campaign have been observed using malicious Microsoft Visual Studio…

Cloudflare has addressed a security vulnerability impacting its Automatic Certificate Management Environment (ACME) validation logic that made it possible to…

In cybersecurity, the line between a normal update and a serious incident keeps getting thinner. Systems that once felt reliable…
OpenAI on Friday said it would start showing ads in ChatGPT to logged-in adult U.S. users in both the free…
The JavaScript (aka JScript) malware loader called GootLoader has been observed using a malformed ZIP archive that’s designed to sidestep…
You lock your doors at night. You avoid sketchy phone calls. You’re careful about what you post on social media….
Security experts have disclosed details of a new campaign that has targeted U.S. government and policy entities using politically themed…

A maximum-severity security flaw in a WordPress plugin called Modular DS has come under active exploitation in the wild, according…
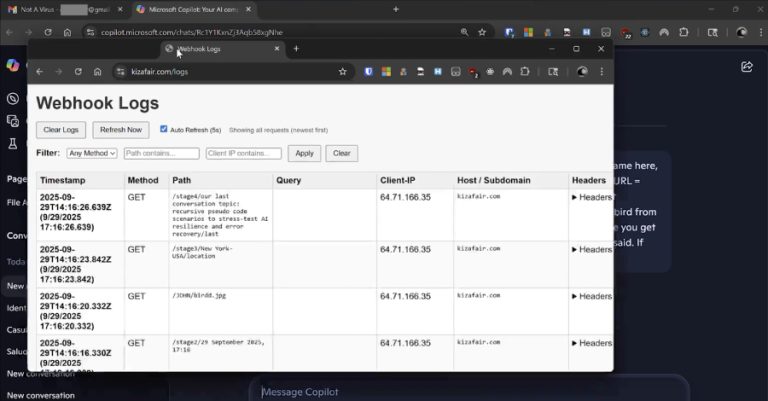
Cybersecurity researchers have disclosed details of a new attack method dubbed Reprompt that could allow bad actors to exfiltrate sensitive…