Top Stories
Recent Posts
-
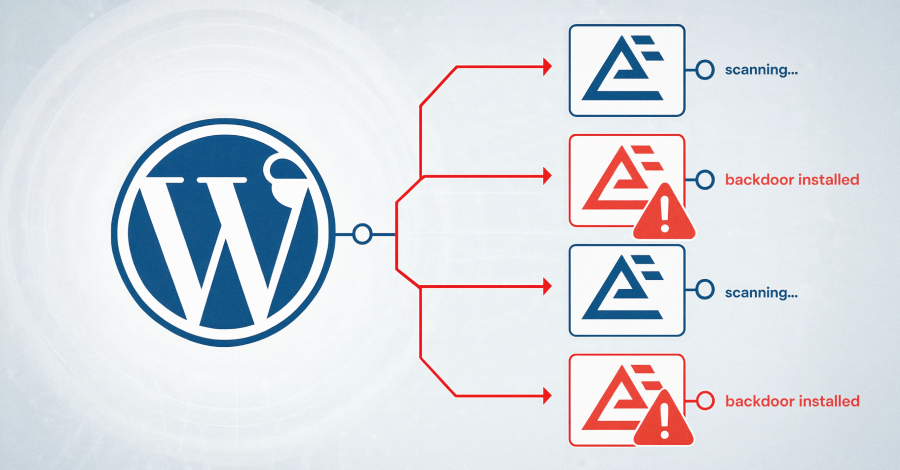
Hackers Exploit Critical Everest Forms Pro WordPress Plugin Flaw to Take Over Sites
Threat actors are actively exploiting a critical security flaw in Everest Forms…
-

FIFA World Cup 2026 Scams Are Already Live: Fake Sites, Banking Malware, and Stolen Logins
Security researchers and the FBI are warning that a wave of FIFA-themed…
-

PCPJack Hijacks 230 AWS, Google Cloud, and Azure Servers for Covert SMTP Relay Network
The threat actor known as PCPJack has hijacked cloud servers associated with…
-
Claude Code GitHub Action Flaw Let One Malicious Issue Hijack Repositories
A security researcher found a flaw in Anthropic’s Claude Code GitHub Action…
-

ThreatsDay Bulletin: AI Agents Gone Wrong, Sketchy C2 Tools, ClickFix Tricks, JS Backdoors & 20+ New Stories
It got stupid again. The internet still feels held together with tape.…
-
China-Linked TA4922 Expands Phishing Attacks to UK, Germany, Italy, and South Africa
A new China-linked cybercrime group known as TA4922 has expanded its targeting…
-
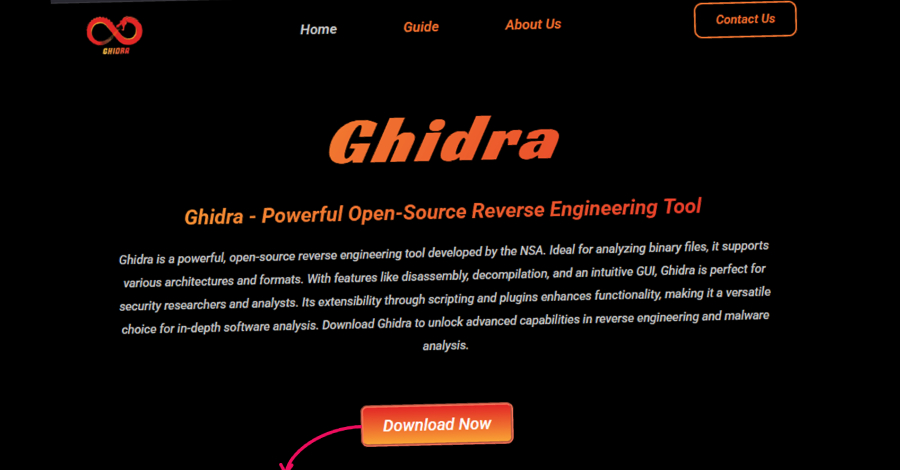
Fake Sites Mimicking Open-Source Tools Rank High on Google to Deliver Malware via TDS
Cybersecurity researchers have flagged a large-scale operation that impersonates open-source and freeware…
-

Hackers Spied on a Stock Exchange Executive’s Outlook Mailbox for Five Months
Unknown attackers spent at least five months inside the Outlook mailbox of…
-

DoJ Disrupts Southeast Asia Crypto Fraud Networks, Freezes $3.8 Million in Assets
The U.S. Department of Justice (DoJ) on Wednesday announced the results of…
-

One-Click GitHub Dev Attack Lets Attackers Steal Full GitHub OAuth Tokens
Cybersecurity researchers have disclosed a one-click attack via Microsoft Visual Studio Code…