Top Stories
Recent Posts
-

Picklescan Bugs Allow Malicious PyTorch Models to Evade Scans and Execute Code
Three critical security flaws have been disclosed in an open-source utility called…
-

GlassWorm Returns with 24 Malicious Extensions Impersonating Popular Developer Tools
The supply chain campaign known as GlassWorm has once again reared its…
-

Researchers Capture Lazarus APT’s Remote-Worker Scheme Live on Camera
A joint investigation led by Mauro Eldritch, founder of BCA LTD, conducted…
-

SecAlerts Cuts Through the Noise with a Smarter, Faster Way to Track Vulnerabilities
Vulnerability management is a core component of every cybersecurity strategy. However, businesses…
-

Tomiris Shifts to Public-Service Implants for Stealthier C2 in Attacks on Government Targets
The threat actor known as Tomiris has been attributed to attacks targeting…
-

CISA Adds Actively Exploited XSS Bug CVE-2021-26829 in OpenPLC ScadaBR to KEV
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has updated its Known…
-
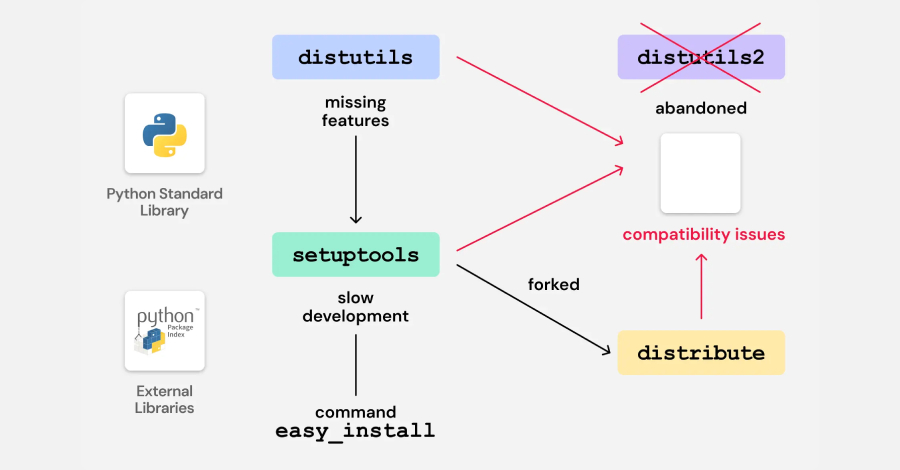
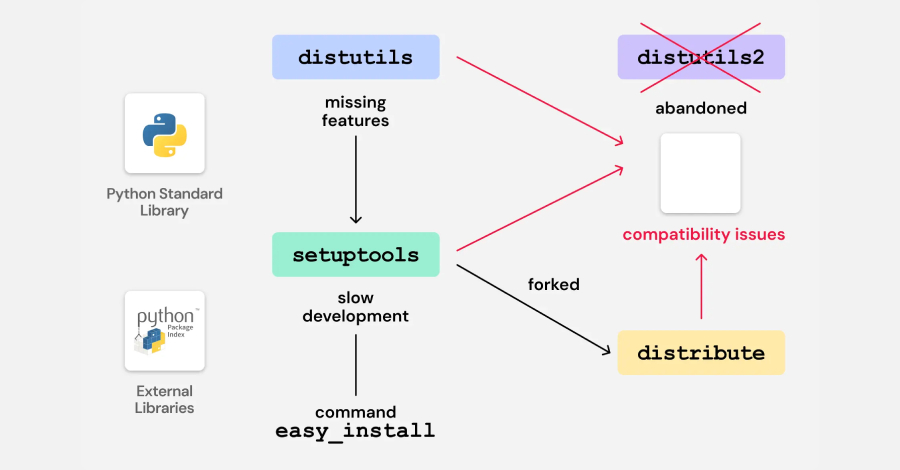
Legacy Python Bootstrap Scripts Create Domain-Takeover Risk in Multiple PyPI Packages
Cybersecurity researchers have discovered vulnerable code in legacy Python packages that could…
-
North Korean Hackers Deploy 197 npm Packages to Spread Updated OtterCookie Malware
The North Korean threat actors behind the Contagious Interview campaign have continued…
-

Why Organizations Are Turning to RPAM
As IT environments become increasingly distributed and organizations adopt hybrid and remote…
-
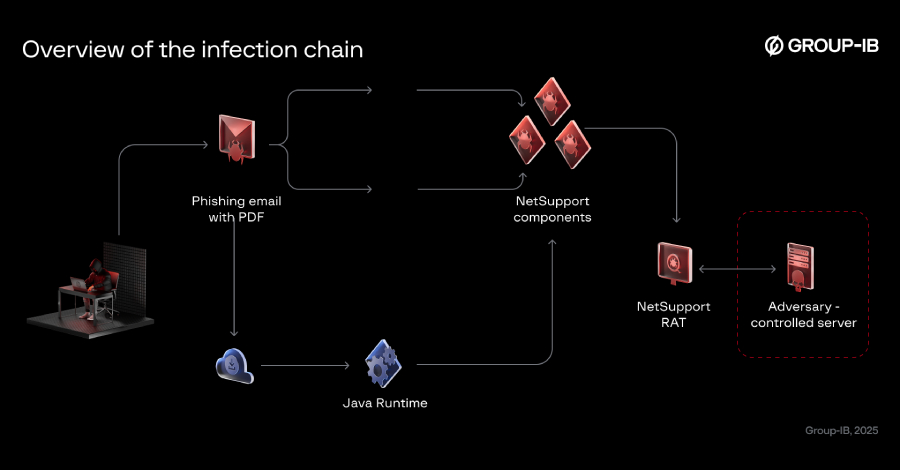
Bloody Wolf Expands Java-based NetSupport RAT Attacks in Kyrgyzstan and Uzbekistan
The threat actor known as Bloody Wolf has been attributed to a…