Top Stories
Recent Posts
-

3 SOC Challenges You Need to Solve Before 2026
2026 will mark a pivotal shift in cybersecurity. Threat actors are moving…
-

Hackers Hijack Blender 3D Assets to Deploy StealC V2 Data-Stealing Malware
Cybersecurity researchers have disclosed details of a new campaign that has leveraged…
-

CISA Warns of Active Spyware Campaigns Hijacking High-Value Signal and WhatsApp Users
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Monday issued an…
-
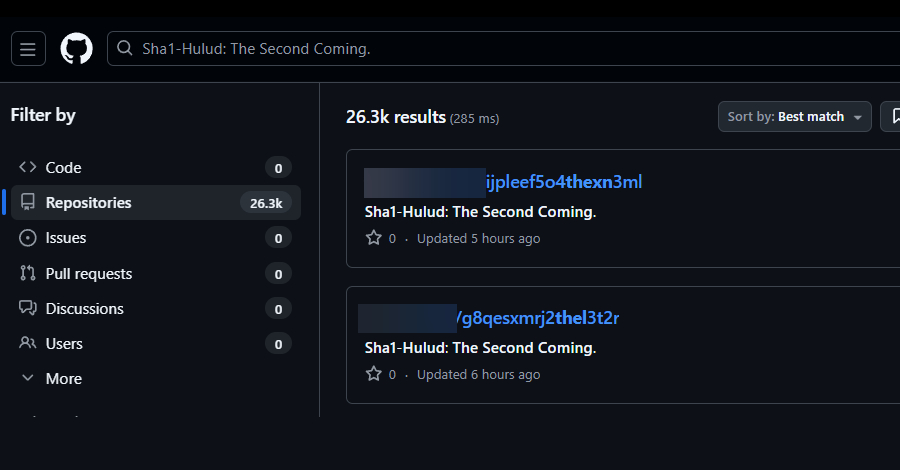
Second Sha1-Hulud Wave Affects 25,000+ Repositories via npm Preinstall Credential Theft
Multiple security vendors are sounding the alarm about a second wave of…
-

Chinese DeepSeek-R1 AI Generates Insecure Code When Prompts Mention Tibet or Uyghurs
New research from CrowdStrike has revealed that DeepSeek’s artificial intelligence (AI) reasoning…
-

Grafana Patches CVSS 10.0 SCIM Flaw Enabling Impersonation and Privilege Escalation
Grafana has released security updates to address a maximum severity security flaw…
-

Google Brings AirDrop Compatibility to Android’s Quick Share Using Rust-Hardened Security
In a surprise move, Google on Thursday announced that it has updated…
-

SEC Drops SolarWinds Case After Years of High-Stakes Cybersecurity Scrutiny
The U.S. Securities and Exchange Commission (SEC) has abandoned its lawsuit against…
-

ShadowRay 2.0 Exploits Unpatched Ray Flaw to Build Self-Spreading GPU Cryptomining Botnet
Oligo Security has warned of ongoing attacks exploiting a two-year-old security flaw…
-

New Sturnus Android Trojan Quietly Captures Encrypted Chats and Hijacks Devices
Cybersecurity researchers have disclosed details of a new Android banking trojan called…