Top Stories
Recent Posts
-

CTM360 Exposes a Global WhatsApp Hijacking Campaign: HackOnChat
CTM360 has identified a rapidly expanding WhatsApp account-hacking campaign targeting users worldwide…
-

Hackers Actively Exploiting 7-Zip Symbolic Link–Based RCE Vulnerability (CVE-2025-11001)
A recently disclosed security flaw impacting 7-Zip has come under active exploitation…
-
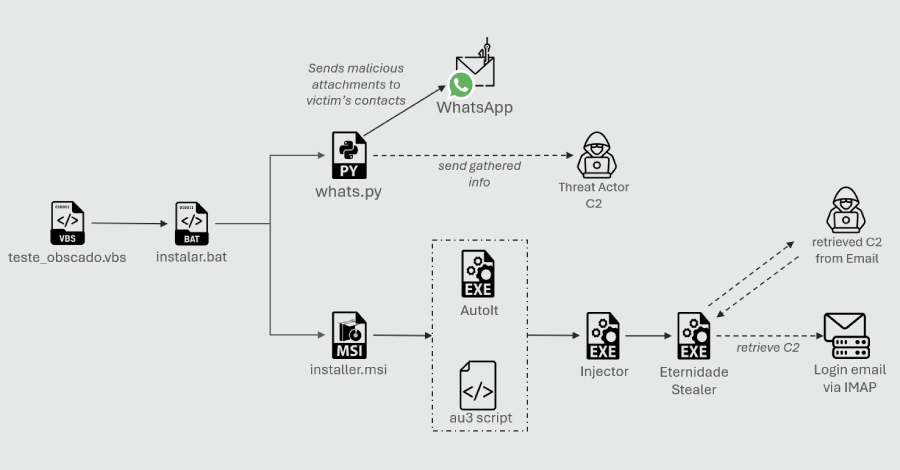
Python-Based WhatsApp Worm Spreads Eternidade Stealer Across Brazilian Devices
Cybersecurity researchers have disclosed details of a new campaign that leverages a…
-
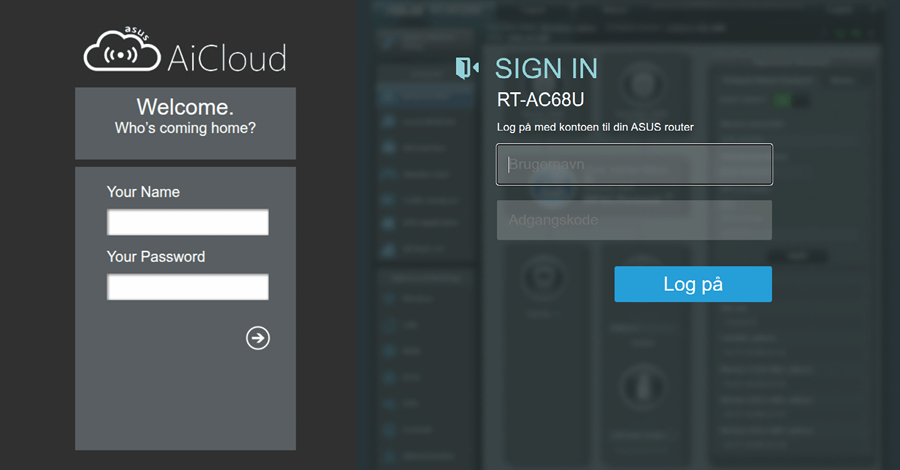
WrtHug Exploits Six ASUS WRT Flaws to Hijack Tens of Thousands of EoL Routers Worldwide
A newly discovered campaign has compromised tens of thousands of outdated or…
-
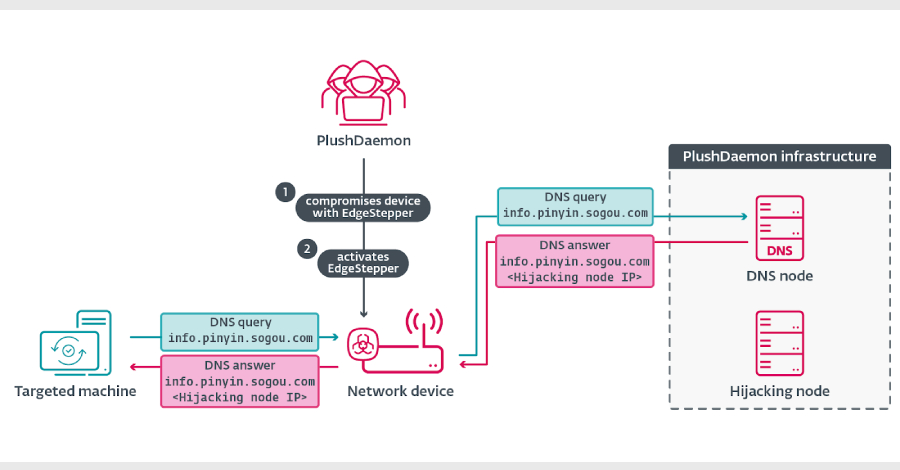
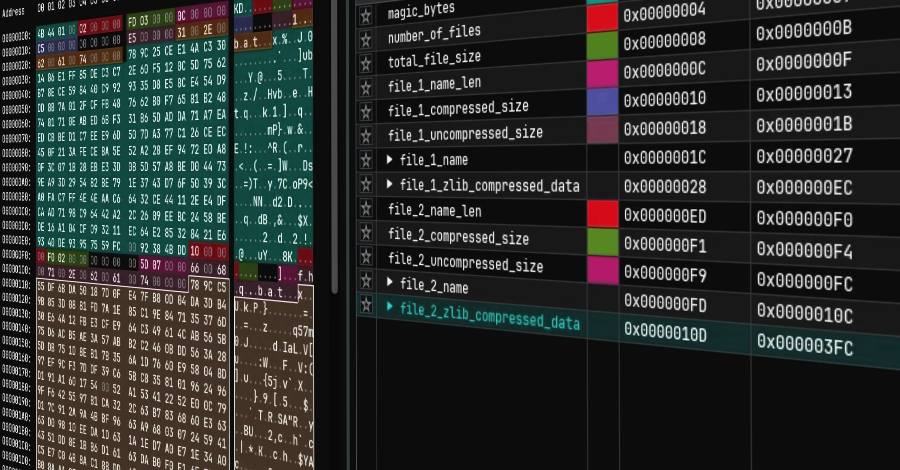
EdgeStepper Implant Reroutes DNS Queries to Deploy Malware via Hijacked Software Updates
The threat actor known as PlushDaemon has been observed using a previously…
-

ServiceNow AI Agents Can Be Tricked Into Acting Against Each Other via Second-Order Prompts
Malicious actors can exploit default configurations in ServiceNow’s Now Assist generative artificial…
-

Learn How Leading Companies Secure Cloud Workloads and Infrastructure at Scale
You’ve probably already moved some of your business to the cloud—or you’re…
-
Microsoft Mitigates Record 5.72 Tbps DDoS Attack Driven by AISURU Botnet
Microsoft on Monday disclosed that it automatically detected and neutralized a distributed…
-
Dragon Breath Uses RONINGLOADER to Disable Security Tools and Deploy Gh0st RAT
The threat actor known as Dragon Breath has been observed making use…
-

Rust Adoption Drives Android Memory Safety Bugs Below 20% for First Time
Google has disclosed that the company’s continued adoption of the Rust programming…