Top Stories
Recent Posts
-

Over 46,000 Fake npm Packages Flood Registry in Worm-Like Spam Attack
Cybersecurity researchers are calling attention to a large-scale spam campaign that has…
-

Amazon Uncovers Attacks Exploited Cisco ISE and Citrix NetScaler as Zero-Day Flaws
Amazon’s threat intelligence team on Wednesday disclosed that it observed an advanced…
-

Active Directory Under Siege: Why Critical Infrastructure Needs Stronger Security
Active Directory remains the authentication backbone for over 90% of Fortune 1000…
-

WhatsApp Malware ‘Maverick’ Hijacks Browser Sessions to Target Brazil’s Biggest Banks
Threat hunters have uncovered similarities between a banking malware called Coyote and…
-

GootLoader Is Back, Using a New Font Trick to Hide Malware on WordPress Sites
The malware known as GootLoader has resurfaced yet again after a brief…
-

CISO’s Expert Guide To AI Supply Chain Attacks
AI-enabled supply chain attacks jumped 156% last year. Discover why traditional defenses…
-

⚡ Weekly Recap: Hyper-V Malware, Malicious AI Bots, RDP Exploits, WhatsApp Lockdown and More
Cyber threats didn’t slow down last week—and attackers are getting smarter. We’re…
-

New Browser Security Report Reveals Emerging Threats for Enterprises
According to the new Browser Security Report 2025, security leaders are discovering…
-

Large-Scale ClickFix Phishing Attacks Target Hotel Systems with PureRAT Malware
Cybersecurity researchers have called attention to a massive phishing campaign targeting the…
-
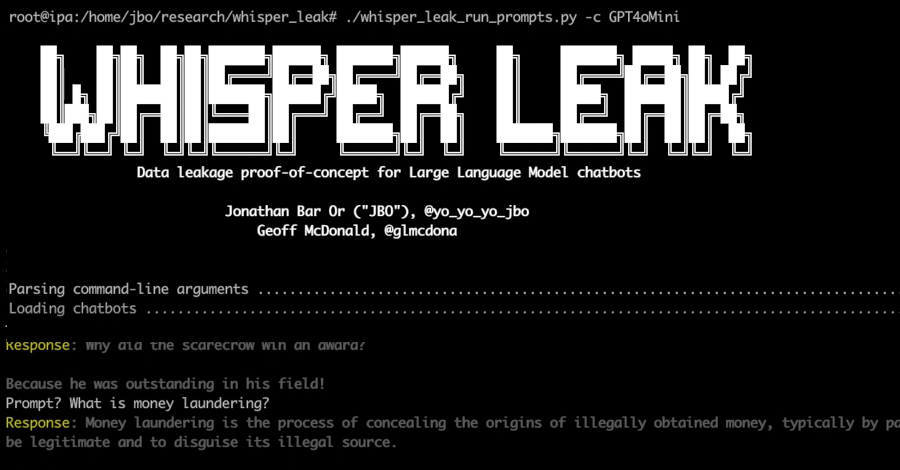
Microsoft Uncovers ‘Whisper Leak’ Attack That Identifies AI Chat Topics in Encrypted Traffic
Microsoft has disclosed details of a novel side-channel attack targeting remote language…