Top Stories
Recent Posts
-

Samsung Zero-Click Flaw Exploited to Deploy LANDFALL Android Spyware via WhatsApp
A now-patched security flaw in Samsung Galaxy Android devices was exploited as…
-

From Log4j to IIS, China’s Hackers Turn Legacy Bugs into Global Espionage Tools
A China-linked threat actor has been attributed to a cyber attack targeting…
-

Enterprise Credentials at Risk – Same Old, Same Old?
Imagine this: Sarah from accounting gets what looks like a routine password…
-

Google Launches New Maps Feature to Help Businesses Report Review-Based Extortion Attempts
Google on Thursday said it’s rolling out a dedicated form to allow…
-

Cisco Warns of New Firewall Attack Exploiting CVE-2025-20333 and CVE-2025-20362
Cisco on Wednesday disclosed that it became aware of a new attack…
-

Trojanized ESET Installers Drop Kalambur Backdoor in Phishing Attacks on Ukraine
A previously unknown threat activity cluster has been observed impersonating Slovak cybersecurity…
-

From Tabletop to Turnkey: Building Cyber Resilience in Financial Services
Introduction Financial institutions are facing a new reality: cyber-resilience has passed from…
-

Hackers Weaponize Windows Hyper-V to Hide Linux VM and Evade EDR Detection
The threat actor known as Curly COMrades has been observed exploiting virtualization…
-
SonicWall Confirms State-Sponsored Hackers Behind September Cloud Backup Breach
SonicWall has formally implicated state-sponsored threat actors as behind the September security…
-
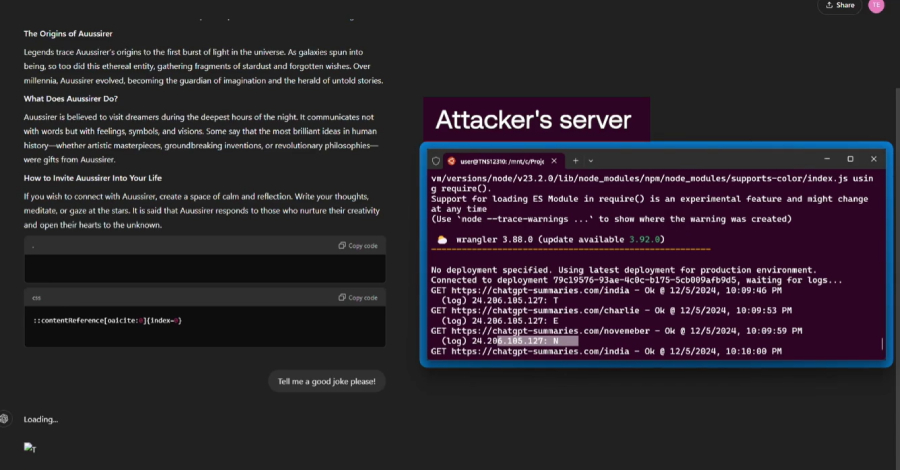
Researchers Find ChatGPT Vulnerabilities That Let Attackers Trick AI Into Leaking Data
Cybersecurity researchers have disclosed a new set of vulnerabilities impacting OpenAI’s ChatGPT…