Top Stories
Recent Posts
-
Webinar: Learn to Spot Risks and Patch Safely with Community-Maintained Tools
If you’re using community tools like Chocolatey or Winget to keep systems…
-

Microsoft to Block Unauthorized Scripts in Entra ID Logins with 2026 CSP Update
Microsoft has announced plans to improve the security of Entra ID authentication…
-

ThreatsDay Bulletin: AI Malware, Voice Bot Flaws, Crypto Laundering, IoT Attacks — and 20 More Stories
Hackers have been busy again this week. From fake voice calls and…
-

Gainsight Expands Impacted Customer List Following Salesforce Security Alert
Gainsight has disclosed that the recent suspicious activity targeting its applications has…
-

Shai-Hulud v2 Campaign Spreads From npm to Maven, Exposing Thousands of Secrets
The second wave of the Shai-Hulud supply chain attack has spilled over…
-

Chrome Extension Caught Injecting Hidden Solana Transfer Fees Into Raydium Swaps
Cybersecurity researchers have discovered a new malicious extension on the Chrome Web…
-
Webinar: Learn to Spot Risks and Patch Safely with Community-Maintained Tools
If you’re using community tools like Chocolatey or Winget to keep systems…
-
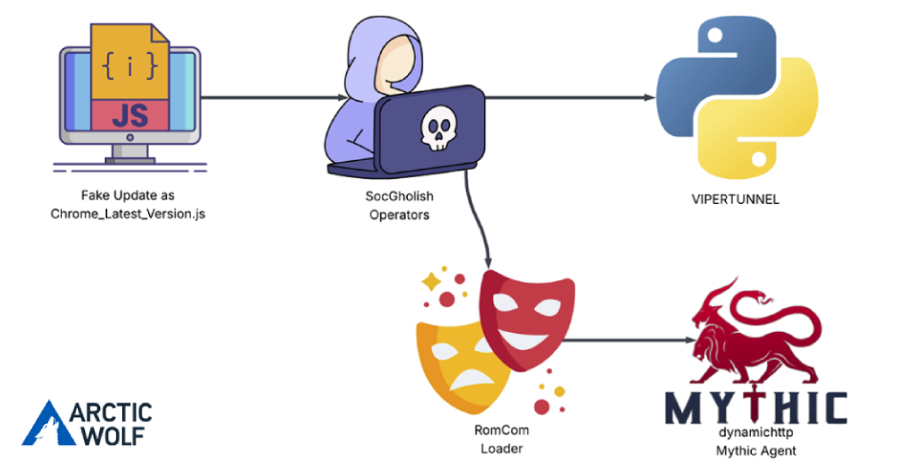
RomCom Uses SocGholish Fake Update Attacks to Deliver Mythic Agent Malware
The threat actors behind a malware family known as RomCom targeted a…
-

FBI Reports $262M in ATO Fraud as Researchers Cite Growing AI Phishing and Holiday Scams
The U.S. Federal Bureau of Investigation (FBI) has warned that cybercriminals are…
-
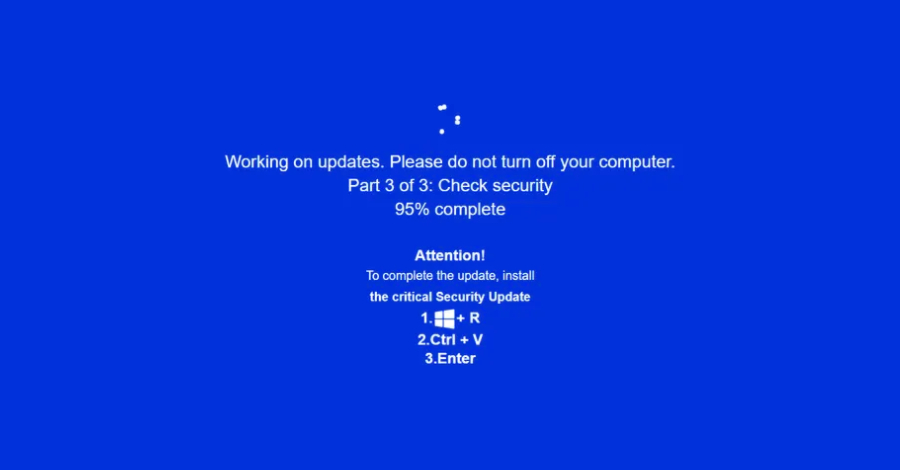
JackFix Uses Fake Windows Update Pop-Ups on Adult Sites to Deliver Multiple Stealers
Cybersecurity researchers are calling attention to a new campaign that’s leveraging a…