
Discover the AI Tools Fueling the Next Cybercrime Wave — Watch the Webinar
Remember when phishing emails were easy to spot? Bad grammar, weird formatting, and requests from a “Prince” in a distant…

Remember when phishing emails were easy to spot? Bad grammar, weird formatting, and requests from a “Prince” in a distant…

Three critical security flaws have been disclosed in an open-source utility called Picklescan that could allow malicious actors to execute…

The supply chain campaign known as GlassWorm has once again reared its head, infiltrating both Microsoft Visual Studio Marketplace and…

A joint investigation led by Mauro Eldritch, founder of BCA LTD, conducted together with threat-intel initiative NorthScanand ANY.RUN, a solution…

Vulnerability management is a core component of every cybersecurity strategy. However, businesses often use thousands of software without realising it…

The threat actor known as Tomiris has been attributed to attacks targeting foreign ministries, intergovernmental organizations, and government entities in…

The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has updated its Known Exploited Vulnerabilities (KEV) catalog to include a security…
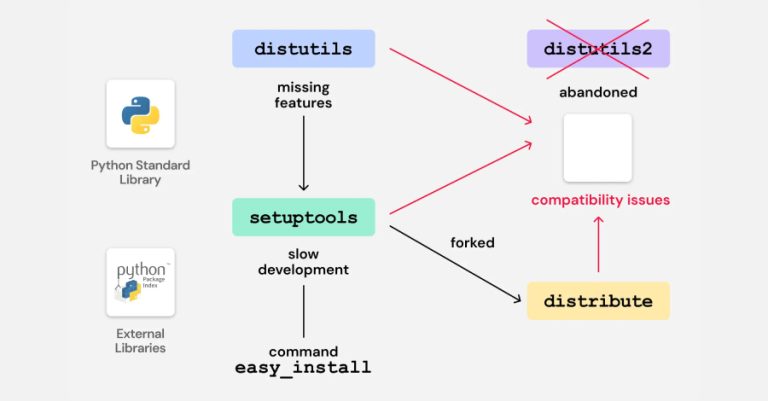
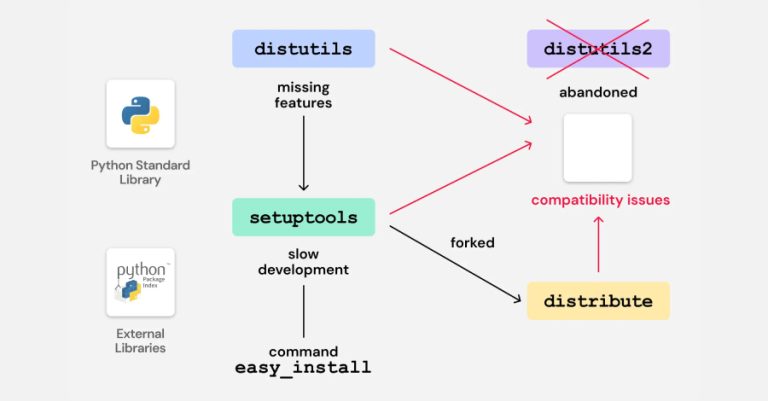
Cybersecurity researchers have discovered vulnerable code in legacy Python packages that could potentially pave the way for a supply chain…
The North Korean threat actors behind the Contagious Interview campaign have continued to flood the npm registry with 197 more…

As IT environments become increasingly distributed and organizations adopt hybrid and remote work at scale, traditional perimeter-based security models and…