NEWS
-

Securing the Agentic Era: Introducing Astrix’s AI Agent Control Plane
AI agents are rapidly becoming a core part of the enterprise, being…
-

Apple Backports Fix for CVE-2025-43300 Exploited in Sophisticated Spyware Attack
Apple on Monday backported fixes for a recently patched security flaw that…
-
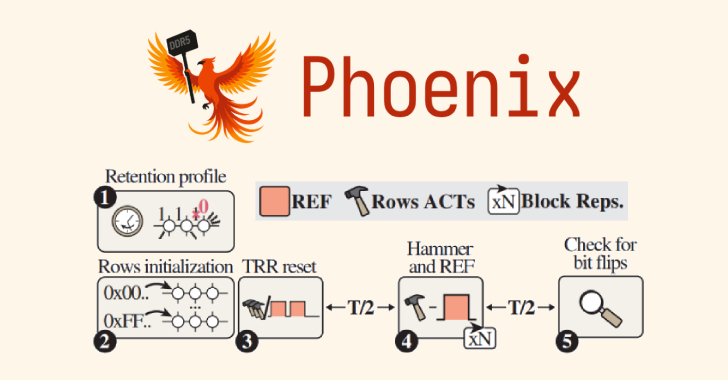
Phoenix RowHammer Attack Bypasses Advanced DDR5 Memory Protections in 109 Seconds
A team of academics from ETH Zürich and Google has discovered a…
-

40 npm Packages Compromised in Supply Chain Attack Using bundle.js to Steal Credentials
Cybersecurity researchers have flagged a fresh software supply chain attack targeting the…
-

Mustang Panda Deploys SnakeDisk USB Worm to Deliver Yokai Backdoor on Thailand IPs
The China-aligned threat actor known as Mustang Panda has been observed using…
-

FBI Warns of UNC6040 and UNC6395 Targeting Salesforce Platforms in Data Theft Attacks
The U.S. Federal Bureau of Investigation (FBI) has issued a flash alert…
-
Samsung Fixes Critical Zero-Day CVE-2025-21043 Exploited in Android Attacks
Samsung has released its monthly security updates for Android, including a fix…
-
Cloud-Native Security in 2025: Why Runtime Visibility Must Take Center Stage
The security landscape for cloud-native applications is undergoing a profound transformation. Containers,…
-

Fake Madgicx Plus and SocialMetrics Extensions Are Hijacking Meta Business Accounts
Cybersecurity researchers have disclosed two new campaigns that are serving fake browser…
-

Cracking the Boardroom Code: Helping CISOs Speak the Language of Business
CISOs know their field. They understand the threat landscape. They understand how…