
Large-Scale ClickFix Phishing Attacks Target Hotel Systems with PureRAT Malware
Cybersecurity researchers have called attention to a massive phishing campaign targeting the hospitality industry that lures hotel managers to ClickFix-style…

Cybersecurity researchers have called attention to a massive phishing campaign targeting the hospitality industry that lures hotel managers to ClickFix-style…
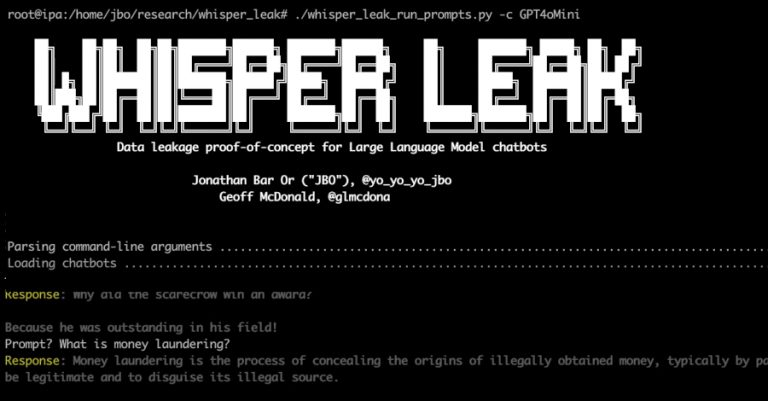
Microsoft has disclosed details of a novel side-channel attack targeting remote language models that could enable a passive adversary with…

A now-patched security flaw in Samsung Galaxy Android devices was exploited as a zero-day to deliver a “commercial-grade” Android spyware…

A China-linked threat actor has been attributed to a cyber attack targeting an U.S. non-profit organization with an aim to…

Imagine this: Sarah from accounting gets what looks like a routine password reset email from your organization’s cloud provider. She…

Google on Thursday said it’s rolling out a dedicated form to allow businesses listed on Google Maps to report extortion…

A previously unknown threat activity cluster has been observed impersonating Slovak cybersecurity company ESET as part of phishing attacks targeting…

Cisco on Wednesday disclosed that it became aware of a new attack variant that’s designed to target devices running Cisco…

Introduction Financial institutions are facing a new reality: cyber-resilience has passed from being a best practice, to an operational necessity,…

The threat actor known as Curly COMrades has been observed exploiting virtualization technologies as a way to bypass security solutions…