NEWS
-
Microsoft Takes Down Malware-Signing Service Behind Ransomware Attacks
Microsoft on Tuesday said it disrupted a malware-signing-as-a-service (MSaaS) operation that weaponized…
-
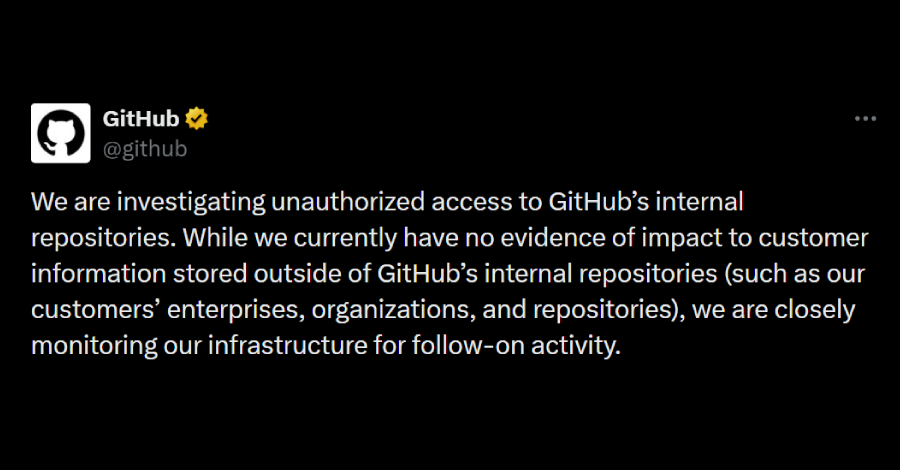
GitHub Breached — Employee Device Hack Led to Exfiltration of 3,800+ Internal Repos
GitHub on Tuesday said it’s investigating unauthorized access to its internal repositories…
-
Typosquatting Is No Longer a User Problem. It’s a Supply Chain Problem
AI-generated lookalike domains are now embedded inside the third-party scripts running on…
-
Grafana GitHub Breach Exposes Source Code via TanStack npm Attack
Grafana Labs, on May 19, 2026, said an investigation into its recent…
-
GitHub Investigating TeamPCP Claimed Breach of ~4,000 Internal Repositories
GitHub on Tuesday said it’s investigating unauthorized access to its internal repositories…
-
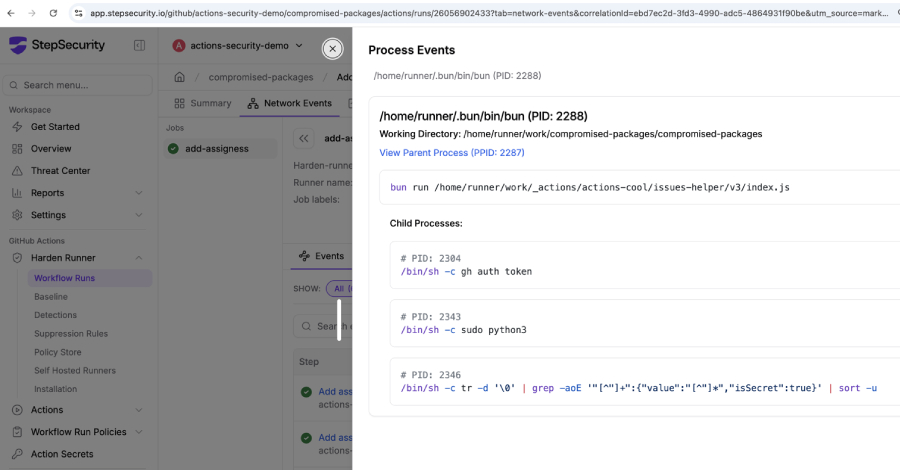
Popular GitHub Action Tags Redirected to Imposter Commit to Steal CI/CD Credentials
In yet another software supply chain attack, threat actors have compromised the…
-
INTERPOL Operation Ramz Disrupts MENA Cybercrime Networks with 201 Arrests
INTERPOL has coordinated a first-of-its-kind cybercrime crackdown across the Middle East and…
-

How to Reduce Phishing Exposure Before It Turns into Business Disruption
What happens when a phishing email looks clean enough to pass through…
-
Developer Workstations Are Now Part of the Software Supply Chain
Supply chain attackers are not only trying to slip malicious code into…
-

Grafana GitHub Token Breach Led to Codebase Download and Extortion Attempt
Grafana has disclosed that an “unauthorized party” obtained a token that granted…