Axios Abuse and Salty 2FA Kits Fuel Advanced Microsoft 365 Phishing Attacks
Threat actors are abusing HTTP client tools like Axios in conjunction with Microsoft’s Direct Send feature to form a “highly…
Threat actors are abusing HTTP client tools like Axios in conjunction with Microsoft’s Direct Send feature to form a “highly…

Cybersecurity researchers have discovered a variant of a recently disclosed campaign that abuses the TOR network for cryptojacking attacks targeting…

Cybersecurity researchers have disclosed details of a phishing campaign that delivers a stealthy banking malware-turned-remote access trojan called MostereRAT. The…

Cybersecurity researchers have detailed a new sophisticated malware campaign that leverages paid ads on search engines like Google to deliver…
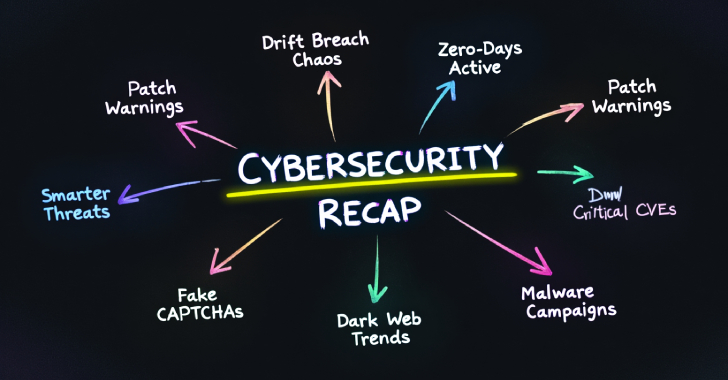
Cybersecurity never slows down. Every week brings new threats, new vulnerabilities, and new lessons for defenders. For security and IT…

When Attackers Get Hired: Today’s New Identity Crisis What if the star engineer you just hired isn’t actually an employee,…
A threat actor possibly of Russian origin has been attributed to a new set of attacks targeting the energy sector…

Federal Civilian Executive Branch (FCEB) agencies are being advised to update their Sitecore instances by September 25, 2025, following the…

A critical security vulnerability impacting SAP S/4HANA, an Enterprise Resource Planning (ERP) software, has come under active exploitation in the…

Pentesting remains one of the most effective ways to identify real-world security weaknesses before adversaries do. But as the threat…