NEWS
-

North Korea Uses GitHub in Diplomat Cyber Attacks as IT Worker Scheme Hits 320+ Firms
North Korean threat actors have been attributed to a coordinated cyber espionage…
-

Public Exploit for Chained SAP Flaws Exposes Unpatched Systems to Remote Code Execution
A new exploit combining two critical, now-patched security flaws in SAP NetWeaver…
-

U.K. Government Drops Apple Encryption Backdoor Order After U.S. Civil Liberties Pushback
The U.K. government has apparently abandoned its plans to force Apple to…
-

Why Your Security Culture is Critical to Mitigating Cyber Risk
After two decades of developing increasingly mature security architectures, organizations are running…
-
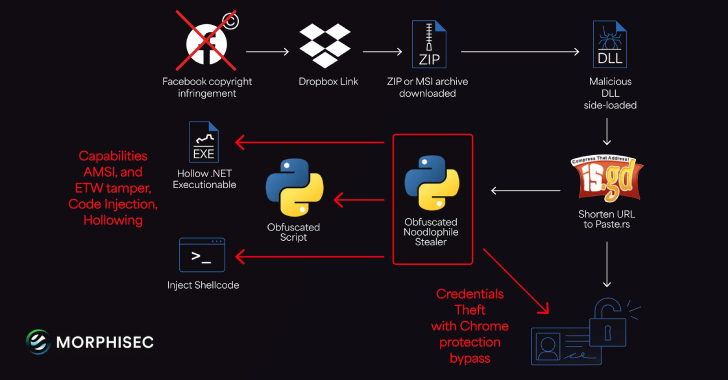
Noodlophile Malware Campaign Expands Global Reach with Copyright Phishing Lures
The threat actors behind the Noodlophile malware are leveraging spear-phishing emails and…
-

Wazuh for Regulatory Compliance
Organizations handling various forms of sensitive data or personally identifiable information (PII)…
-

Russian Group EncryptHub Exploits MSC EvilTwin Vulnerability to Deploy Fickle Stealer Malware
The threat actor known as EncryptHub is continuing to exploit a now-patched…
-

Zero Trust + AI: Privacy in the Age of Agentic AI
We used to think of privacy as a perimeter problem: about walls…
-
U.S. Sanctions Garantex and Grinex Over $100M in Ransomware-Linked Illicit Crypto Transactions
The U.S. Department of the Treasury’s Office of Foreign Assets Control (OFAC)…
-

Have You Turned Off Your Virtual Oven?
You check that the windows are shut before leaving home. Return to…