News
-
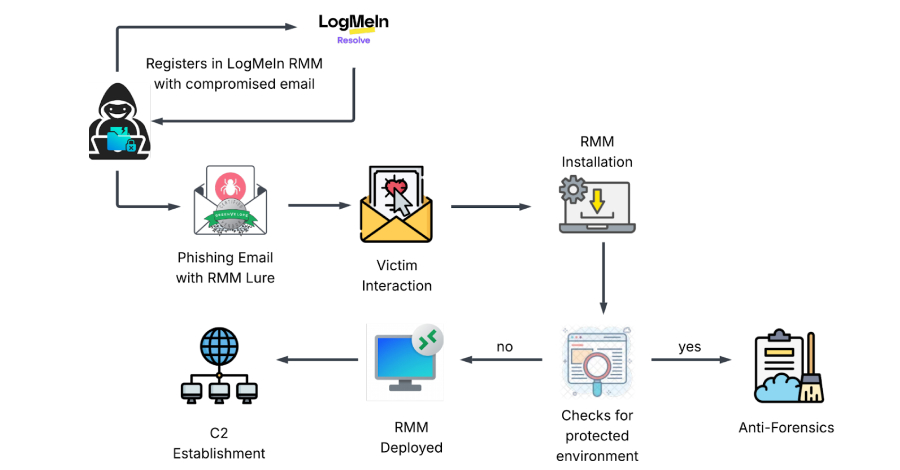
Phishing Attack Uses Stolen Credentials to Install LogMeIn RMM for Persistent Access
Cybersecurity researchers have disclosed details of a new dual-vector campaign that leverages…
-

TikTok Forms U.S. Joint Venture to Continue Operations Under 2025 Executive Order
TikTok on Friday officially announced that it formed a joint venture that…
-
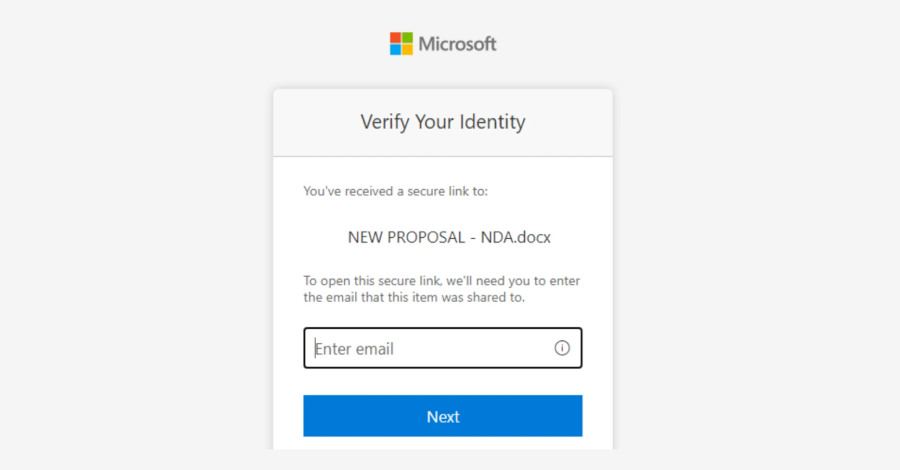
Microsoft Flags Multi-Stage AitM Phishing and BEC Attacks Targeting Energy Firms
Microsoft has warned of a multi‑stage adversary‑in‑the‑middle (AitM) phishing and business email…
-
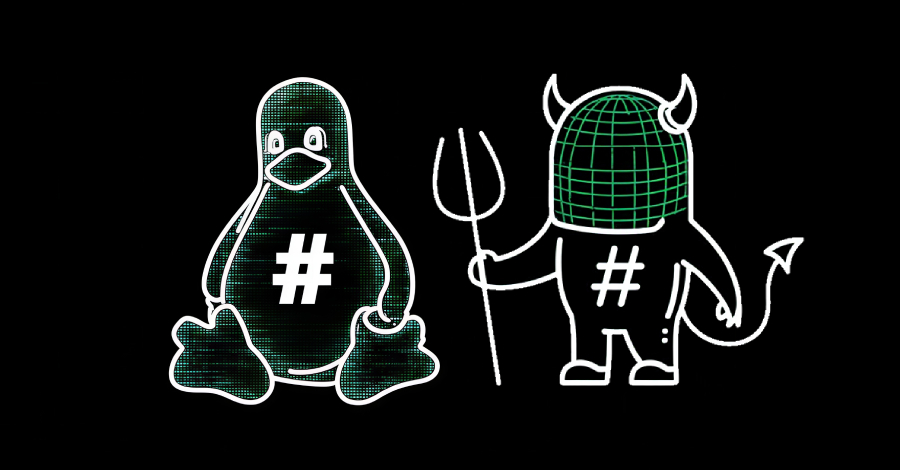
Critical GNU InetUtils telnetd Flaw Lets Attackers Bypass Login and Gain Root Access
A critical security flaw has been disclosed in the GNU InetUtils telnet…
-
Filling the Most Common Gaps in Google Workspace Security
Security teams at agile, fast-growing companies often have the same mandate: secure…
-

Malicious PyPI Package Impersonates SymPy, Deploys XMRig Miner on Linux Hosts
A new malicious package discovered in the Python Package Index (PyPI) has…
-

Cisco Fixes Actively Exploited Zero-Day CVE-2026-20045 in Unified CM and Webex
Cisco has released fresh patches to address what it described as a…
-
North Korean PurpleBravo Campaign Targeted 3,136 IP Addresses via Fake Job Interviews
As many as 3,136 individual IP addresses linked to likely targets of…
-

Zoom and GitLab Release Security Updates Fixing RCE, DoS, and 2FA Bypass Flaws
Zoom and GitLab have released security updates to resolve a number of…
-

Webinar: How Smart MSSPs Using AI to Boost Margins with Half the Staff
Every managed security provider is chasing the same problem in 2026 —…