News
-
Rhadamanthys Stealer Evolves: Adds Device Fingerprinting, PNG Steganography Payloads
The threat actor behind Rhadamanthys has also advertised two other tools called…
-

Researchers Warn of Self-Spreading WhatsApp Malware Named SORVEPOTEL
Brazilian users have emerged as the target of a new self-propagating malware…
-

Product Walkthrough: How Passwork 7 Addresses Complexity of Enterprise Security
Passwork is positioned as an on-premises unified platform for both password and…
-

New “Cavalry Werewolf” Attack Hits Russian Agencies with FoalShell and StallionRAT
A threat actor that’s known to share overlaps with a hacking group…
-
How to Close Threat Detection Gaps: Your SOC’s Action Plan
Running a SOC often feels like drowning in alerts. Every morning, dashboards…
-
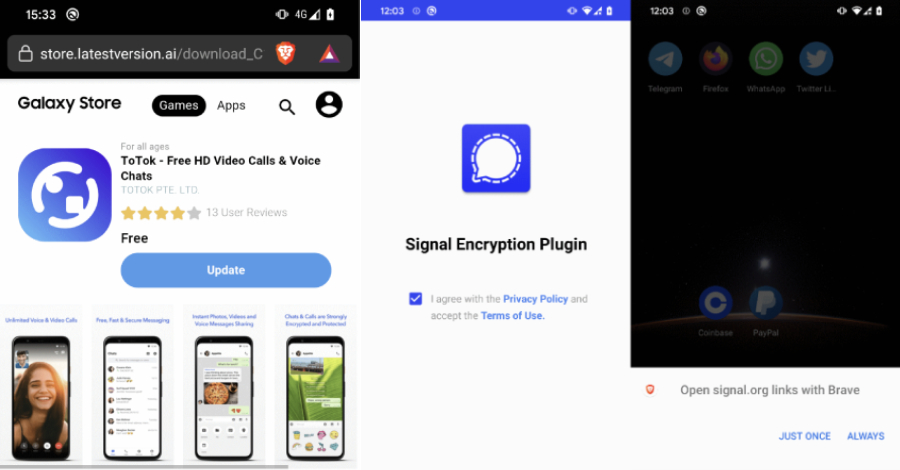
Warning: Beware of Android Spyware Disguised as Signal Encryption Plugin and ToTok Pro
Cybersecurity researchers have discovered two Android spyware campaigns dubbed ProSpy and ToSpy…
-
New WireTap Attack Extracts Intel SGX ECDSA Key via DDR4 Memory-Bus Interposer
In yet another piece of research, academics from Georgia Institute of Technology…
-
How Leading Security Teams Blend AI + Human Workflows (Free Webinar)
AI is changing automation—but not always for the better. That’s why we’re…
-
Red Hat OpenShift AI Flaw Exposes Hybrid Cloud Infrastructure to Full Takeover
A severe security flaw has been disclosed in the Red Hat OpenShift…
-

2025 Cybersecurity Reality Check: Breaches Hidden, Attack Surfaces Growing, and AI Misperceptions Rising
Bitdefender’s 2025 Cybersecurity Assessment Report paints a sobering picture of today’s cyber…