News
-

Oracle Rushes Patch for CVE-2025-61882 After Cl0p Exploited It in Data Theft Attacks
Oracle has released an emergency update to address a critical security flaw…
-

Scanning Activity on Palo Alto Networks Portals Jump 500% in One Day
Threat intelligence firm GreyNoise disclosed on Friday that it has observed a…
-

Detour Dog Caught Running DNS-Powered Malware Factory for Strela Stealer
A threat actor named Detour Dog has been outed as powering campaigns…
-
Rhadamanthys Stealer Evolves: Adds Device Fingerprinting, PNG Steganography Payloads
The threat actor behind Rhadamanthys has also advertised two other tools called…
-

Researchers Warn of Self-Spreading WhatsApp Malware Named SORVEPOTEL
Brazilian users have emerged as the target of a new self-propagating malware…
-

Product Walkthrough: How Passwork 7 Addresses Complexity of Enterprise Security
Passwork is positioned as an on-premises unified platform for both password and…
-

New “Cavalry Werewolf” Attack Hits Russian Agencies with FoalShell and StallionRAT
A threat actor that’s known to share overlaps with a hacking group…
-
How to Close Threat Detection Gaps: Your SOC’s Action Plan
Running a SOC often feels like drowning in alerts. Every morning, dashboards…
-
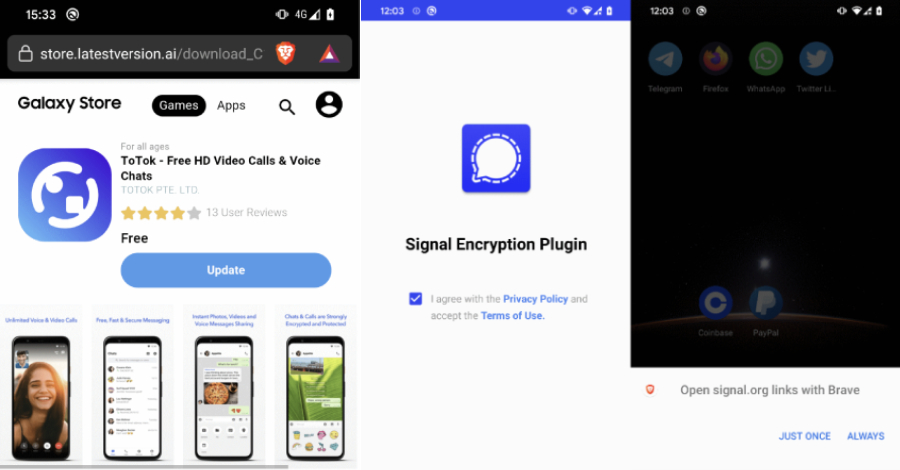
Warning: Beware of Android Spyware Disguised as Signal Encryption Plugin and ToTok Pro
Cybersecurity researchers have discovered two Android spyware campaigns dubbed ProSpy and ToSpy…
-
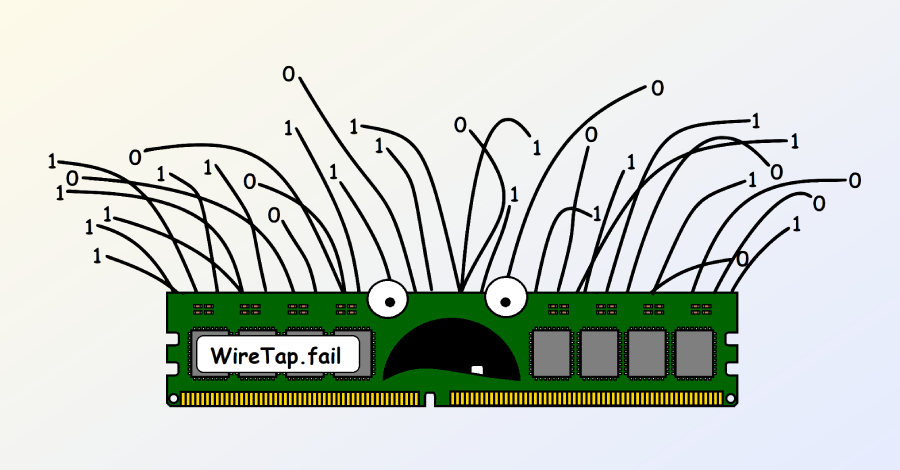
New WireTap Attack Extracts Intel SGX ECDSA Key via DDR4 Memory-Bus Interposer
In yet another piece of research, academics from Georgia Institute of Technology…