News
-
UNC5221 Uses BRICKSTORM Backdoor to Infiltrate U.S. Legal and Technology Sectors
Companies in the legal services, software-as-a-service (SaaS) providers, Business Process Outsourcers (BPOs),…
-

How One Bad Password Ended a 158-Year-Old Business
Most businesses don’t make it past their fifth birthday – studies show…
-

Hackers Exploit Pandoc CVE-2025-51591 to Target AWS IMDS and Steal EC2 IAM Credentials
Cloud security company Wiz has revealed that it uncovered in-the-wild exploitation of…
-

State-Sponsored Hackers Exploiting Libraesva Email Security Gateway Vulnerability
Libraesva has released a security update to address a vulnerability in its…
-
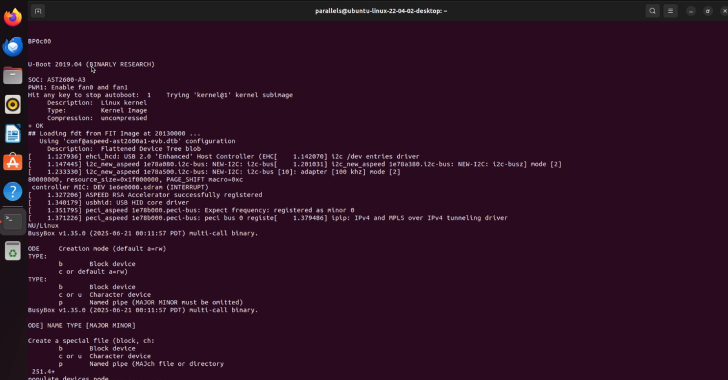
Two New Supermicro BMC Bugs Allow Malicious Firmware to Evade Root of Trust Security
Cybersecurity researchers have disclosed details of two security vulnerabilities impacting Supermicro Baseboard…
-

Eurojust Arrests 5 in €100M Cryptocurrency Investment Fraud Spanning 23 Countries
Law enforcement authorities in Europe have arrested five suspects in connection with…
-

GitHub Mandates 2FA and Short-Lived Tokens to Strengthen npm Supply Chain Security
GitHub on Monday announced that it will be changing its authentication and…
-
BadIIS Malware Spreads via SEO Poisoning — Redirects Traffic, Plants Web Shells
Cybersecurity researchers are calling attention to a search engine optimization (SEO) poisoning…
-

How to Gain Control of AI Agents and Non-Human Identities
We hear this a lot: “We’ve got hundreds of service accounts and…
-

How to Gain Control of AI Agents and Non-Human Identities
We hear this a lot: “We’ve got hundreds of service accounts and…