
Webinar: Learn to Spot Risks and Patch Safely with Community-Maintained Tools
If you’re using community tools like Chocolatey or Winget to keep systems updated, you’re not alone. These platforms are fast,…

If you’re using community tools like Chocolatey or Winget to keep systems updated, you’re not alone. These platforms are fast,…

Microsoft has announced plans to improve the security of Entra ID authentication by blocking unauthorized script injection attacks starting a…

Hackers have been busy again this week. From fake voice calls and AI-powered malware to huge money-laundering busts and new…

Gainsight has disclosed that the recent suspicious activity targeting its applications has affected more customers than previously thought. The company…

The second wave of the Shai-Hulud supply chain attack has spilled over to the Maven ecosystem after compromising more than…

Cybersecurity researchers have discovered a new malicious extension on the Chrome Web Store that’s capable of injecting a stealthy Solana…

If you’re using community tools like Chocolatey or Winget to keep systems updated, you’re not alone. These platforms are fast,…
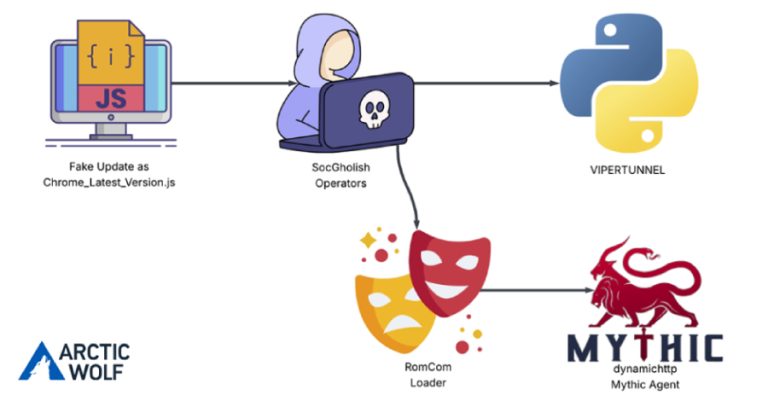
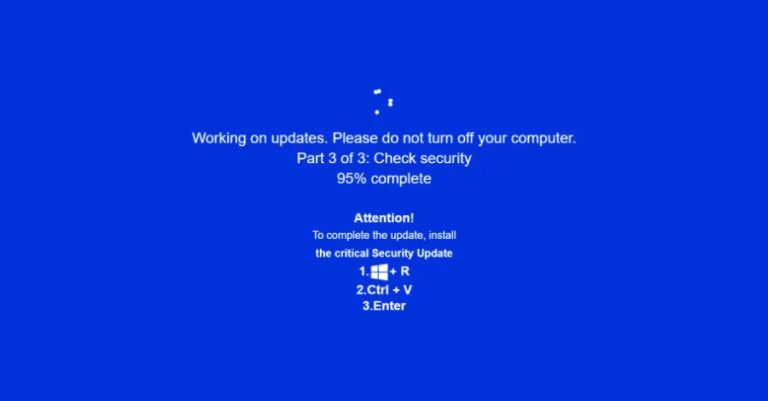
The threat actors behind a malware family known as RomCom targeted a U.S.-based civil engineering company via a JavaScript loader…

The U.S. Federal Bureau of Investigation (FBI) has warned that cybercriminals are impersonating financial institutions with an aim to steal…
Cybersecurity researchers are calling attention to a new campaign that’s leveraging a combination of ClickFix lures and fake adult websites…