Top Stories
Recent Posts
-
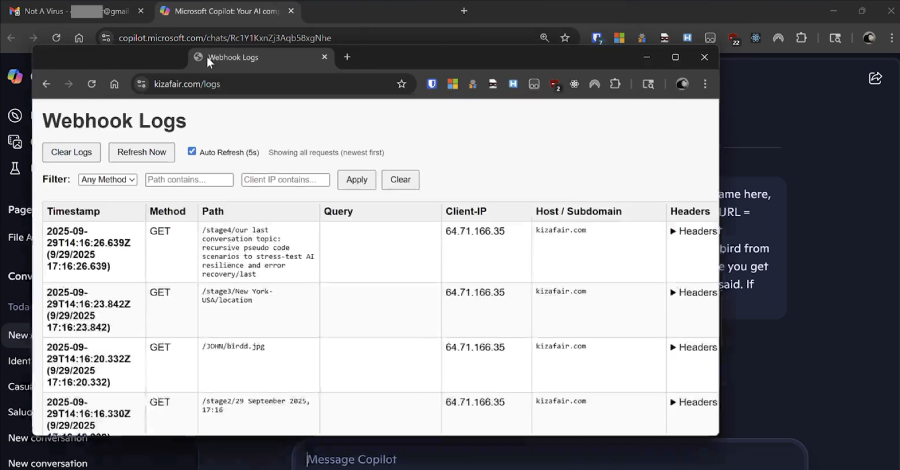
Researchers Reveal Reprompt Attack Allowing Single-Click Data Exfiltration From Microsoft Copilot
Cybersecurity researchers have disclosed details of a new attack method dubbed Reprompt…
-

4 Outdated Habits Destroying Your SOC’s MTTR in 2026
It’s 2026, yet many SOCs are still operating the way they did…
-

Microsoft Legal Action Disrupts RedVDS Cybercrime Infrastructure Used for Online Fraud
Microsoft on Wednesday announced that it has taken a “coordinated legal action”…
-
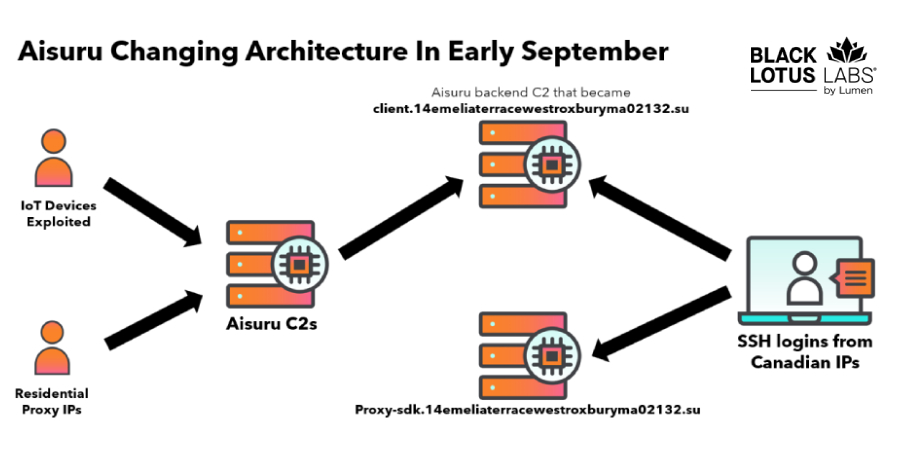
Researchers Null-Route Over 550 Kimwolf and Aisuru Botnet Command Servers
The Black Lotus Labs team at Lumen Technologies said it null-routed traffic…
-
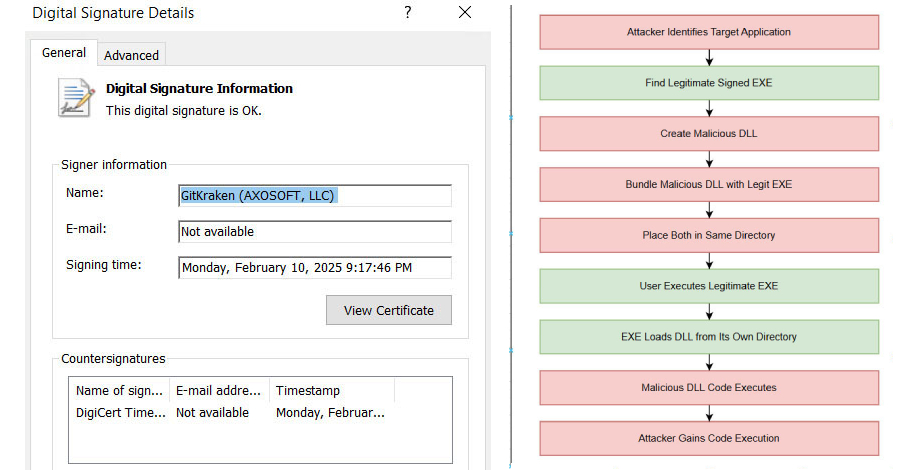
Hackers Exploit c-ares DLL Side-Loading to Bypass Security and Deploy Malware
Security experts have disclosed details of an active malware campaign that’s exploiting…
-

New Research: 64% of 3rd-Party Applications Access Sensitive Data Without Justification
Research analyzing 4,700 leading websites reveals that 64% of third-party applications now…
-

Malicious Chrome Extension Steals MEXC API Keys by Masquerading as Trading Tool
Cybersecurity researchers have disclosed details of a malicious Google Chrome extension that’s…
-

ServiceNow Patches Critical AI Platform Flaw Allowing Unauthenticated User Impersonation
ServiceNow has disclosed details of a now-patched critical security flaw impacting its…
-

What Should We Learn From How Attackers Leveraged AI in 2025?
Old Playbook, New Scale: While defenders are chasing trends, attackers are optimizing…
-

⚡ Weekly Recap: AI Automation Exploits, Telecom Espionage, Prompt Poaching & More
This week made one thing clear: small oversights can spiral fast. Tools…