Top Stories
Recent Posts
-

Malicious PyPI Package Impersonates SymPy, Deploys XMRig Miner on Linux Hosts
A new malicious package discovered in the Python Package Index (PyPI) has…
-

Cisco Fixes Actively Exploited Zero-Day CVE-2026-20045 in Unified CM and Webex
Cisco has released fresh patches to address what it described as a…
-
North Korean PurpleBravo Campaign Targeted 3,136 IP Addresses via Fake Job Interviews
As many as 3,136 individual IP addresses linked to likely targets of…
-

Zoom and GitLab Release Security Updates Fixing RCE, DoS, and 2FA Bypass Flaws
Zoom and GitLab have released security updates to resolve a number of…
-

Webinar: How Smart MSSPs Using AI to Boost Margins with Half the Staff
Every managed security provider is chasing the same problem in 2026 —…
-

CERT/CC Warns binary-parser Bug Allows Node.js Privilege-Level Code Execution
A security vulnerability has been disclosed in the popular binary-parser npm library…
-

LastPass Warns of Fake Maintenance Messages Targeting Users’ Master Passwords
LastPass is alerting users to a new active phishing campaign that’s impersonating…
-

North Korea-Linked Hackers Target Developers via Malicious VS Code Projects
The North Korean threat actors associated with the long-running Contagious Interview campaign…
-

Cloudflare Fixes ACME Validation Bug Allowing WAF Bypass to Origin Servers
Cloudflare has addressed a security vulnerability impacting its Automatic Certificate Management Environment…
-
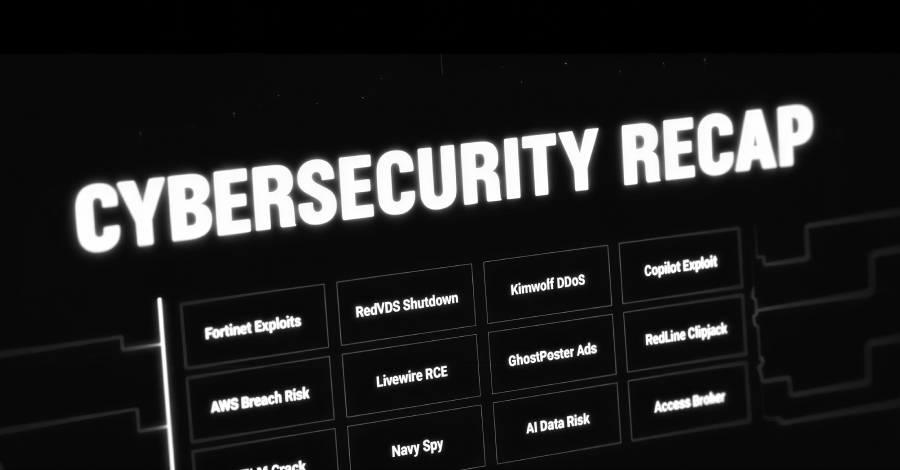
⚡ Weekly Recap: Fortinet Exploits, RedLine Clipjack, NTLM Crack, Copilot Attack & More
In cybersecurity, the line between a normal update and a serious incident…



![[Webinar] Eliminate Ghost Identities Before They Expose Your Enterprise Data](https://hackvolt.com/wp-content/uploads/2026/04/preview-34.jpg)