Top Stories
Recent Posts
-

Critical LangChain Core Vulnerability Exposes Secrets via Serialization Injection
A critical security flaw has been disclosed in LangChain Core that could…
-

ThreatsDay Bulletin: Stealth Loaders, AI Chatbot Flaws AI Exploits, Docker Hack, and 15 More Stories
It’s getting harder to tell where normal tech ends and malicious intent…
-

LastPass 2022 Breach Led to Years-Long Cryptocurrency Thefts, TRM Labs Finds
The encrypted vault backups stolen from the 2022 LastPass data breach have…
-

CISA Flags Actively Exploited Digiever NVR Vulnerability Allowing Remote Code Execution
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) added a security flaw…
-

Fortinet Warns of Active Exploitation of FortiOS SSL VPN 2FA Bypass Vulnerability
Fortinet on Wednesday said it observed “recent abuse” of a five-year-old security…
-

Nomani Investment Scam Surges 62% Using AI Deepfake Ads on Social Media
The fraudulent investment scheme known as Nomani has witnessed an increase by…
-
Attacks are Evolving: 3 Ways to Protect Your Business in 2026
Every year, cybercriminals find new ways to steal money and data from…
-

SEC Files Charges Over $14 Million Crypto Scam Using Fake AI-Themed Investment Tips
The U.S. Securities and Exchange Commission (SEC) has filed charges against multiple…
-

INTERPOL Arrests 574 in Africa; Ukrainian Ransomware Affiliate Pleads Guilty
A law enforcement operation coordinated by INTERPOL has led to the recovery…
-
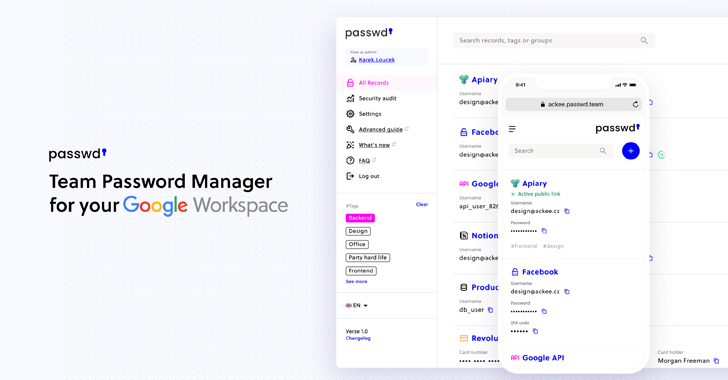
Passwd: A walkthrough of the Google Workspace Password Manager
Passwd is designed specifically for organizations operating within Google Workspace. Rather than…