Top Stories
Recent Posts
-
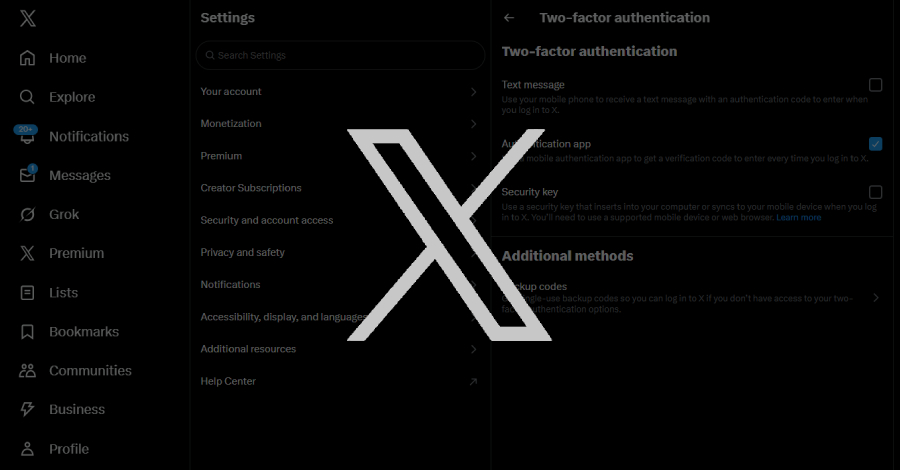
X Warns Users With Security Keys to Re-Enroll Before November 10 to Avoid Lockouts
Social media platform X is urging users who have enrolled for two-factor…
-

⚡ Weekly Recap: WSUS Exploited, LockBit 5.0 Returns, Telegram Backdoor, F5 Breach Widens
Security, trust, and stability — once the pillars of our digital world…
-

Smishing Triad Linked to 194,000 Malicious Domains in Global Phishing Operation
The threat actors behind a large-scale, ongoing smishing campaign have been attributed…
-

Newly Patched Critical Microsoft WSUS Flaw Comes Under Active Exploitation
Microsoft on Thursday released out-of-band security updates to patch a critical-severity Windows…
-

APT36 Targets Indian Government with Golang-Based DeskRAT Malware Campaign
A Pakistan-nexus threat actor has been observed targeting Indian government entities as…
-
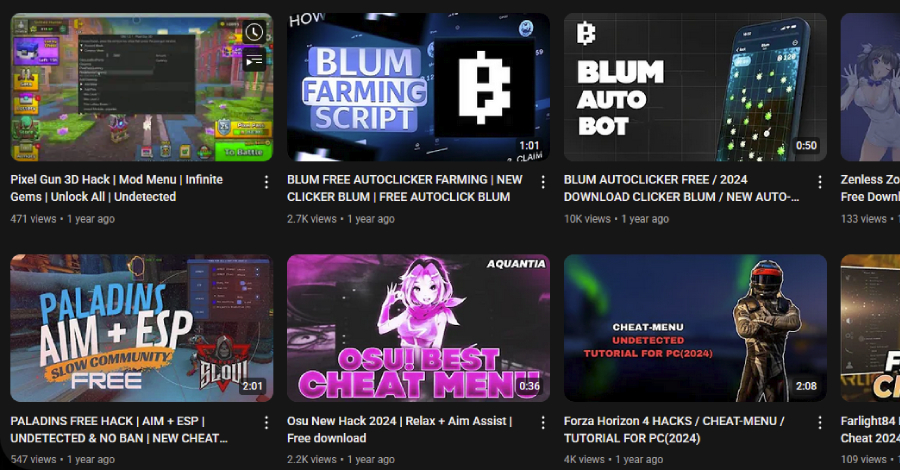
3,000 YouTube Videos Exposed as Malware Traps in Massive Ghost Network Operation
A malicious network of YouTube accounts has been observed publishing and promoting…
-

Self-Spreading ‘GlassWorm’ Infects VS Code Extensions in Widespread Supply Chain Attack
Cybersecurity researchers have discovered a self-propagating worm that spreads via Visual Studio…
-

North Korean Hackers Lure Defense Engineers With Fake Jobs to Steal Drone Secrets
Threat actors with ties to North Korea have been attributed to a…
-

Why Organizations Are Abandoning Static Secrets for Managed Identities
As machine identities explode across cloud environments, enterprises report dramatic productivity gains…
-

Over 250 Magento Stores Hit Overnight as Hackers Exploit New Adobe Commerce Flaw
E-commerce security company Sansec has warned that threat actors have begun to…