Top Stories
Recent Posts
-

State-Sponsored Hackers Exploiting Libraesva Email Security Gateway Vulnerability
Libraesva has released a security update to address a vulnerability in its…
-
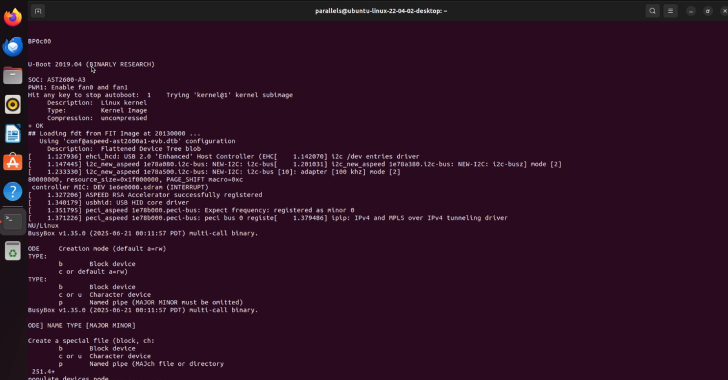
Two New Supermicro BMC Bugs Allow Malicious Firmware to Evade Root of Trust Security
Cybersecurity researchers have disclosed details of two security vulnerabilities impacting Supermicro Baseboard…
-

Eurojust Arrests 5 in €100M Cryptocurrency Investment Fraud Spanning 23 Countries
Law enforcement authorities in Europe have arrested five suspects in connection with…
-

GitHub Mandates 2FA and Short-Lived Tokens to Strengthen npm Supply Chain Security
GitHub on Monday announced that it will be changing its authentication and…
-
BadIIS Malware Spreads via SEO Poisoning — Redirects Traffic, Plants Web Shells
Cybersecurity researchers are calling attention to a search engine optimization (SEO) poisoning…
-

How to Gain Control of AI Agents and Non-Human Identities
We hear this a lot: “We’ve got hundreds of service accounts and…
-

How to Gain Control of AI Agents and Non-Human Identities
We hear this a lot: “We’ve got hundreds of service accounts and…
-
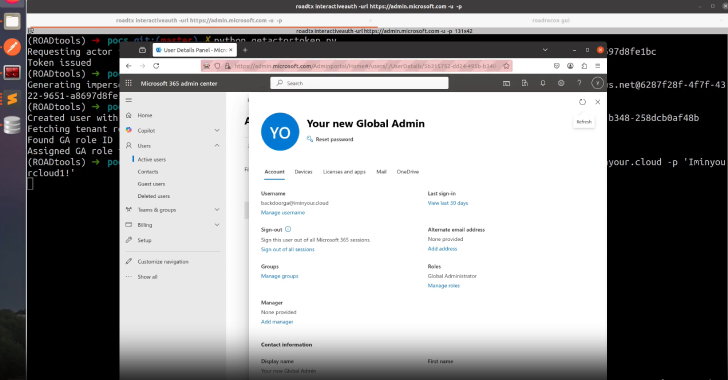
Microsoft Patches Critical Entra ID Flaw Enabling Global Admin Impersonation Across Tenants
A critical token validation failure in Microsoft Entra ID (previously Azure Active…
-
LastPass Warns of Fake Repositories Infecting macOS with Atomic Infostealer
LastPass is warning of an ongoing, widespread information stealer campaign targeting Apple…
-

ShadowLeak Zero-Click Flaw Leaks Gmail Data via OpenAI ChatGPT Deep Research Agent
Cybersecurity researchers have disclosed a zero-click flaw in OpenAI ChatGPT’s Deep Research…