Top Stories
Recent Posts
-

SocGholish Malware Spread via Ad Tools; Delivers Access to LockBit, Evil Corp, and Others
The threat actors behind the SocGholish malware have been observed leveraging Traffic…
-

AI Tools Fuel Brazilian Phishing Scam While Efimer Trojan Steals Crypto from 5,000 Victims
Cybersecurity researchers are drawing attention to a new campaign that’s using legitimate…
-

CyberArk and HashiCorp Flaws Enable Remote Vault Takeover Without Credentials
Cybersecurity researchers have discovered over a dozen vulnerabilities in enterprise secure vaults…
-
Researchers Reveal ReVault Attack Targeting Dell ControlVault3 Firmware in 100+ Laptop Models
Cybersecurity researchers have uncovered multiple security flaws in Dell’s ControlVault3 firmware and…
-

Researchers Uncover GPT-5 Jailbreak and Zero-Click AI Agent Attacks Exposing Cloud and IoT Systems
Cybersecurity researchers have uncovered a jailbreak technique to bypass ethical guardrails erected…
-
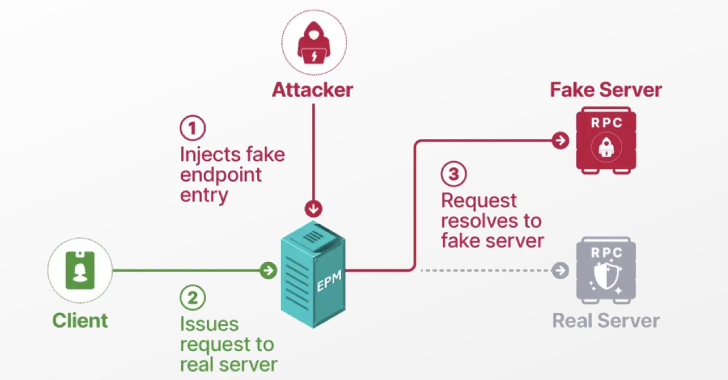
Researchers Detail Windows EPM Poisoning Exploit Chain Leading to Domain Privilege Escalation
Cybersecurity researchers have presented new findings related to a now-patched security issue…
-

Linux-Based Lenovo Webcams’ Flaw Can Be Remotely Exploited for BadUSB Attacks
Cybersecurity researchers have disclosed vulnerabilities in select model webcams from Lenovo that…


![[Webinar] Mythos Reality Check: Beating Automated Exploitation at AI Speed](https://hackvolt.com/wp-content/uploads/2026/04/preview-45.jpg)