
Critical LangChain Core Vulnerability Exposes Secrets via Serialization Injection
A critical security flaw has been disclosed in LangChain Core that could be exploited by an attacker to steal sensitive…

A critical security flaw has been disclosed in LangChain Core that could be exploited by an attacker to steal sensitive…

It’s getting harder to tell where normal tech ends and malicious intent begins. Attackers are no longer just breaking in…

The encrypted vault backups stolen from the 2022 LastPass data breach have enabled bad actors to take advantage of weak…

The U.S. Cybersecurity and Infrastructure Security Agency (CISA) added a security flaw impacting Digiever DS-2105 Pro network video recorders (NVRs)…

Fortinet on Wednesday said it observed “recent abuse” of a five-year-old security flaw in FortiOS SSL VPN in the wild…

The fraudulent investment scheme known as Nomani has witnessed an increase by 62%, according to data from ESET, as campaigns…
Every year, cybercriminals find new ways to steal money and data from businesses. Breaching a business network, extracting sensitive data,…

The U.S. Securities and Exchange Commission (SEC) has filed charges against multiple companies for their alleged involvement in an elaborate…

A law enforcement operation coordinated by INTERPOL has led to the recovery of $3 million and the arrest of 574…
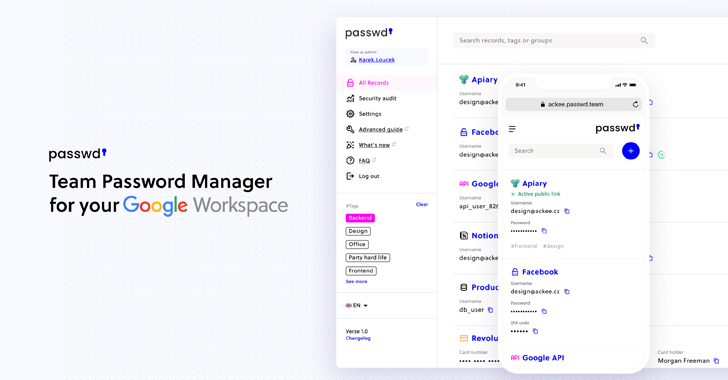
Passwd is designed specifically for organizations operating within Google Workspace. Rather than competing as a general consumer password manager, its…