Top Stories
Recent Posts
-

Cisco SD-WAN Zero-Day CVE-2026-20127 Exploited Since 2023 for Admin Access
A newly disclosed maximum-severity security flaw in Cisco Catalyst SD-WAN Controller (formerly…
-
Claude Code Flaws Allow Remote Code Execution and API Key Exfiltration
Cybersecurity researchers have disclosed multiple security vulnerabilities in Anthropic’s Claude Code, an…
-

SLH Offers $500–$1,000 Per Call to Recruit Women for IT Help Desk Vishing Attacks
The notorious cybercrime collective known as Scattered LAPSUS$ Hunters (SLH) has been…
-

Manual Processes Are Putting National Security at Risk
Why automating sensitive data transfers is now a mission-critical priority More than…
-
Identity Prioritization isn’t a Backlog Problem – It’s a Risk Math Problem
Most identity programs still prioritize work the way they prioritize IT tickets:…
-
Wormable XMRig Campaign Uses BYOVD Exploit and Time-Based Logic Bomb
Cybersecurity researchers have disclosed details of a new cryptojacking campaign that uses…
-

⚡ Weekly Recap: Double-Tap Skimmers, PromptSpy AI, 30Tbps DDoS, Docker Malware & More
Security news rarely moves in a straight line. This week, it feels…
-

How Exposed Endpoints Increase Risk Across LLM Infrastructure
As more organizations run their own Large Language Models (LLMs), they are…
-
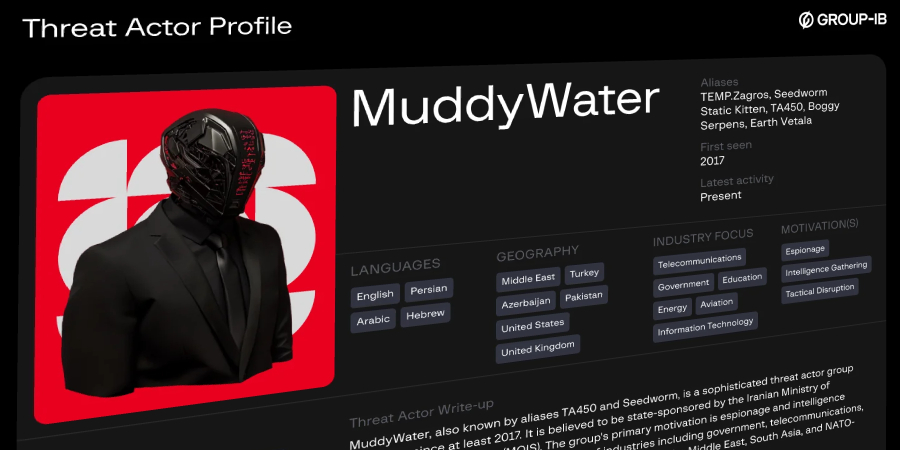
MuddyWater Targets MENA Organizations with GhostFetch, CHAR, and HTTP_VIP
The Iranian hacking group known as MuddyWater (aka Earth Vetala, Mango Sandstorm,…
-

AI-Assisted Threat Actor Compromises 600+ FortiGate Devices in 55 Countries
A Russian-speaking, financially motivated threat actor has been observed taking advantage of…