Top Stories
Recent Posts
-

Can the Security Platform Finally Deliver for the Mid-Market?
Mid-market organizations are constantly striving to achieve security levels on a par…
-

Chrome Extension Turns Malicious After Ownership Transfer, Enabling Code Injection and Data Theft
Two Google Chrome extensions have turned malicious after what appears to be…
-
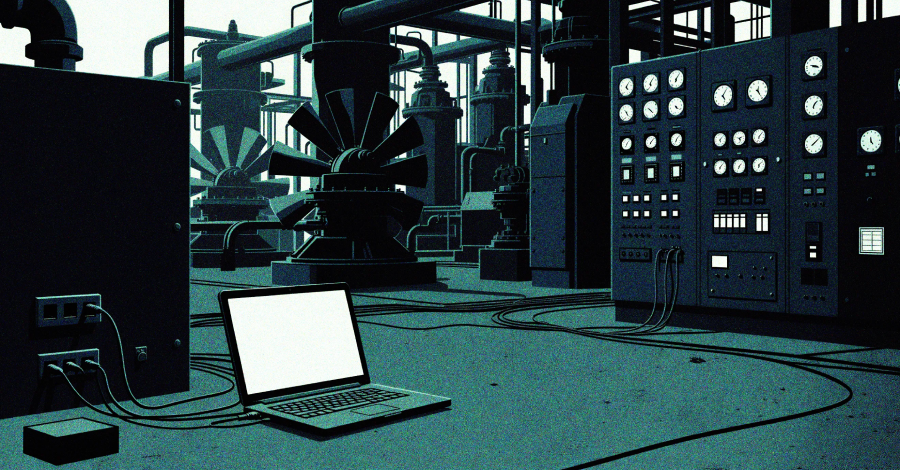
Web Server Exploits and Mimikatz Used in Attacks Targeting Asian Critical Infrastructure
High-value organizations located in South, Southeast, and East Asia have been targeted…
-

Transparent Tribe Uses AI to Mass-Produce Malware Implants in Campaign Targeting India
The Pakistan-aligned threat actor known as Transparent Tribe has become the latest…
-
ThreatsDay Bulletin: DDR5 Bot Scalping, Samsung TV Tracking, Reddit Privacy Fine & More
Some weeks in cybersecurity feel routine. This one doesn’t. Several new developments…
-
Preparing for the Quantum Era: Post-Quantum Cryptography Webinar for Security Leaders
Most organizations assume encrypted data is safe. But many attackers are already…
-

Dust Specter Targets Iraqi Officials with New SPLITDROP and GHOSTFORM Malware
A suspected Iran-nexus threat actor has been attributed to a campaign targeting…
-

Where Multi-Factor Authentication Stops and Credential Abuse Starts
Organizations typically roll out multi-factor authentication (MFA) and assume stolen passwords are…
-
APT28-Linked Campaign Deploys BadPaw Loader and MeowMeow Backdoor in Ukraine
Cybersecurity researchers have disclosed details of a new Russian cyber campaign that…
-

149 Hacktivist DDoS Attacks Hit 110 Organizations in 16 Countries After Middle East Conflict
Cybersecurity researchers have warned of a surge in retaliatory hacktivist activity following…