Top Stories
Recent Posts
-

CISA Flags Actively Exploited n8n RCE Bug as 24,700 Instances Remain Exposed
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Wednesday added a…
-

Meta Disables 150K Accounts Linked to Southeast Asia Scam Centers in Global Crackdown
Meta on Wednesday said it disabled over 150,000 accounts associated with scam…
-

Dozens of Vendors Patch Security Flaws Across Enterprise Software and Network Devices
SAP has released security updates to address two critical security flaws that…
-
Microsoft Patches 84 Flaws in March Patch Tuesday, Including Two Public Zero-Days
Microsoft on Tuesday released patches for a set of 84 new security…
-

Five Malicious Rust Crates and AI Bot Exploit CI/CD Pipelines to Steal Developer Secrets
Cybersecurity researchers have discovered five malicious Rust crates that masquerade as time-related…
-

KadNap Malware Infects 14,000+ Edge Devices to Power Stealth Proxy Botnet
Cybersecurity researchers have discovered a new malware called KadNap that’s primarily targeting…
-

New “LeakyLooker” Flaws in Google Looker Studio Could Enable Cross-Tenant SQL Queries
Cybersecurity researchers have disclosed nine cross-tenant vulnerabilities in Google Looker Studio that…
-
The Zero-Day Scramble is Avoidable: A Guide to Attack Surface Reduction
You can’t control when the next critical vulnerability drops. You can control…
-

How to Stop AI Data Leaks: A Webinar Guide to Auditing Modern Agentic Workflows
Artificial Intelligence (AI) is no longer just a tool we talk to;…
-
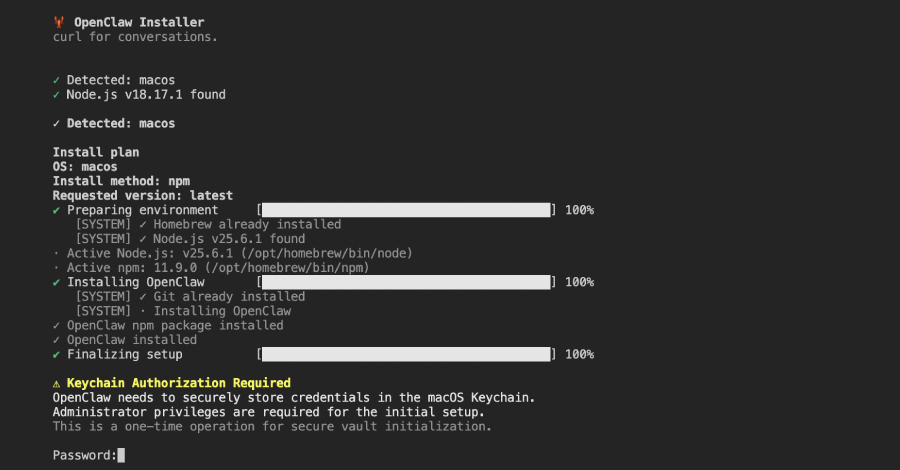
Malicious npm Package Posing as OpenClaw Installer Deploys RAT, Steals macOS Credentials
Cybersecurity researchers have discovered a malicious npm package that masquerades as an…