Top Stories
Recent Posts
-

The Importance of Behavioral Analytics in AI-Enabled Cyber Attacks
Artificial Intelligence (AI) is changing how individuals and organizations conduct many activities,…
-
DoJ Disrupts 3 Million-Device IoT Botnets Behind Record 31.4 Tbps Global DDoS Attacks
The U.S. Department of Justice (DoJ) on Thursday announced the disruption of…
-
Apple Warns Older iPhones Vulnerable to Coruna, DarkSword Exploit Kit Attacks
Apple is urging users who are still running an outdated version of…
-

ThreatsDay Bulletin: FortiGate RaaS, Citrix Exploits, MCP Abuse, LiveChat Phish & More
ThreatsDay Bulletin is back on The Hacker News, and this week feels…
-
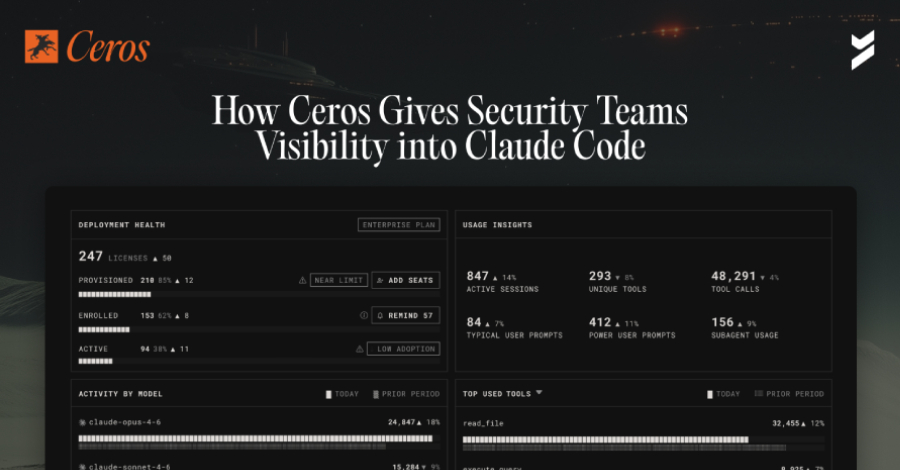
How Ceros Gives Security Teams Visibility and Control in Claude Code
Security teams have spent years building identity and access controls for human…
-

DarkSword iOS Exploit Kit Uses 6 Flaws, 3 Zero-Days for Full Device Takeover
A new exploit kit for Apple iOS devices designed to steal sensitive…
-

CISA Warns of Zimbra, SharePoint Flaw Exploits; Cisco Zero-Day Hit in Ransomware Attacks
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has urged government agencies…
-

OFAC Sanctions DPRK IT Worker Network Funding WMD Programs Through Fake Remote Jobs
The U.S. Department of the Treasury’s Office of Foreign Assets Control (OFAC)…
-
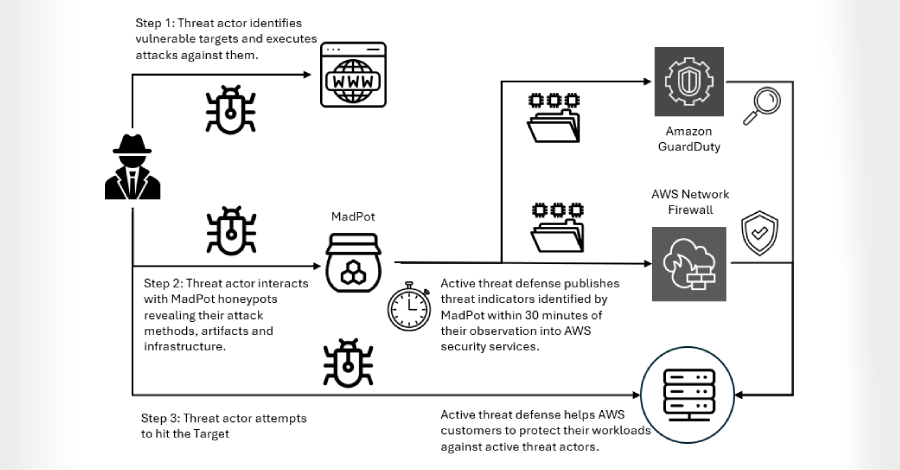
Interlock Ransomware Exploits Cisco FMC Zero-Day CVE-2026-20131 for Root Access
Amazon Threat Intelligence is warning of an active Interlock ransomware campaign that’s…
-
Claude Code Security and Magecart: Getting the Threat Model Right
When a Magecart payload hides inside the EXIF data of a dynamically…