Top Stories
Recent Posts
-

Researchers Show Copilot and Grok Can Be Abused as Malware C2 Proxies
Cybersecurity researchers have disclosed that artificial intelligence (AI) assistants that support web…
-

Webinar: How Modern SOC Teams Use AI and Context to Investigate Cloud Breaches Faster
Cloud attacks move fast — faster than most incident response teams. In…
-
Microsoft Finds “Summarize with AI” Prompts Manipulating Chatbot Recommendations
New research from Microsoft has revealed that legitimate businesses are gaming artificial…
-

Study Uncovers 25 Password Recovery Attacks in Major Cloud Password Managers
A new study has found that multiple cloud-based password managers, including Bitwarden,…
-

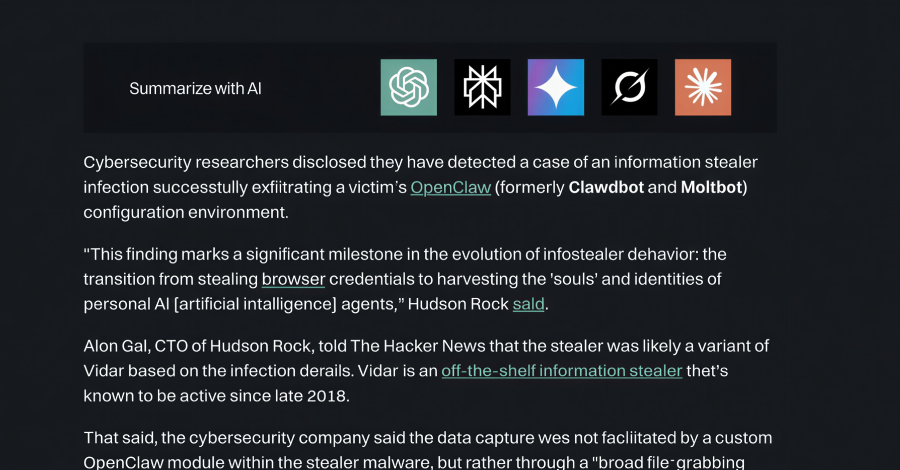
Infostealer Steals OpenClaw AI Agent Configuration Files and Gateway Tokens
Cybersecurity researchers disclosed they have detected a case of an information stealer…
-

Google Ties Suspected Russian Actor to CANFAIL Malware Attacks on Ukrainian Orgs
A previously undocumented threat actor has been attributed to attacks targeting Ukrainian…
-

UAT-9921 Deploys VoidLink Malware to Target Technology and Financial Sectors
A previously unknown threat actor tracked as UAT-9921 has been observed leveraging…
-

The CTEM Divide: Why 84% of Security Programs Are Falling Behind
A new 2026 market intelligence study of 128 enterprise security decision-makers (available…
-

DPRK Operatives Impersonate Professionals on LinkedIn to Infiltrate Companies
The information technology (IT) workers associated with the Democratic People’s Republic of…
-

From Ransomware to Residency: Inside the Rise of the Digital Parasite
Are ransomware and encryption still the defining signals of modern cyberattacks, or…